You are performing an ISMS audit at a residential nursing home that provides healthcare services. The next step in your audit plan is to verify the information security incident management process. The IT Security Manager presents the information security incident management procedure and explains that the process is based on ISO/IEC 27035-1:2016.
You are performing an ISMS audit at a residential nursing home that provides healthcare services. The next step in your audit plan is to verify the information security incident management process. The IT Security Manager presents the information security incident management procedure and explains that the process is based on ISO/IEC 27035-1:2016.
You review the document and notice a statement "any information security weakness, event, and incident should be reported to the Point of Contact (PoC) within 1 hour after identification". When interviewing staff, you found that there were differences in the understanding of the meaning of "weakness, event, and incident".
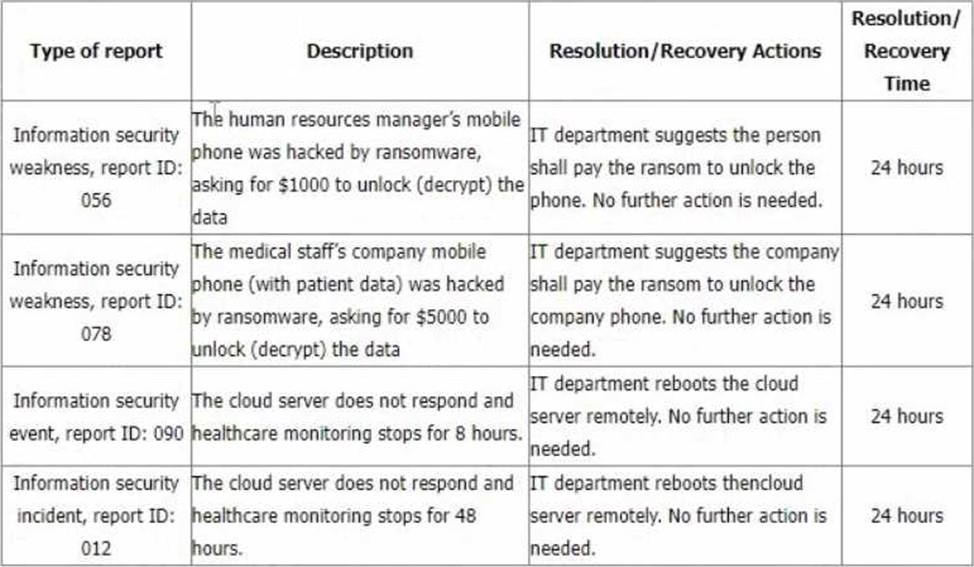
You sample incident report records from the event tracking system for the last 6 months with summarized results in the following table.
You would like to further investigate other areas to collect more audit evidence. Select two options that will not be in your audit trail.
A. Collect more evidence on how and when the Human Resources manager pays the ransom fee to unlock personal mobile data, i.e., credit card, and bank transfer. (Relevant to control A.5.26)
B. Collect more evidence on what the service requirements of healthcare monitoring are. (Relevant to clause 4.2)
C. Collect more evidence on how the organization determined no further action was needed after the incident. (Relevant to control A.5.26)
D. Collect more evidence on how the organisation determined the incident recovery time. (Relevant to control A.5.27)
E. Collect more evidence on the incident recovery procedures. (Relevant to control A.5.26)
F. Collect more evidence by interviewing more staff about their understanding of the reporting process. (Relevant to control A.6.8)
G. Collect more evidence on how and when the company pays the ransom fee to unlock the company’s mobile phone and data, i.e., credit card, and bank transfer. (Relevant to control A.5.26)
Answer: B, G
Explanation:
According to ISO/IEC 27001:2022, which specifies the requirements for establishing, implementing, maintaining and continually improving an information security management system (ISMS), clause 4.2 requires an organization to determine the needs and expectations of interested parties that are relevant to its ISMS1. This includes identifying the legal, regulatory, contractual and other requirements that apply to its information security activities1. Therefore, collecting more evidence on what the service requirements of healthcare monitoring are may not be relevant to verifying the information security incident management process, as it is not directly related to the audit objective or criteria. This option will not be in the audit trail.
Latest ISO-IEC-27001 Lead Auditor Dumps Valid Version with 100 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

