Which Azure Blob storage settings should you use?
Topic 3, City Power & Light
Case study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. When you are ready to answer a question, click the Question button to return to the question.
Background
City Power & Light company provides electrical infrastructure monitoring solutions for homes and businesses. The company is migrating solutions to Azure.
Current environment
Architecture overview
The company has a public website located at http://www.cpandl.com/. The site is a single-page web application that runs in Azure App Service on Linux. The website uses files stored in Azure Storage and cached in Azure Content Delivery Network (CDN) to serve static content.
API Management and Azure Function App functions are used to process and store data in Azure Database for PostgreSQL. API Management is used to broker communications to the Azure Function app functions for Logic app integration. Logic apps are used to orchestrate the data processing while Service Bus and Event Grid handle messaging and events.
The solution uses Application Insights, Azure Monitor, and Azure Key Vault.
Architecture diagram
The company has several applications and services that support their business. The company plans to implement serverless computing where possible.
The overall architecture is shown below.
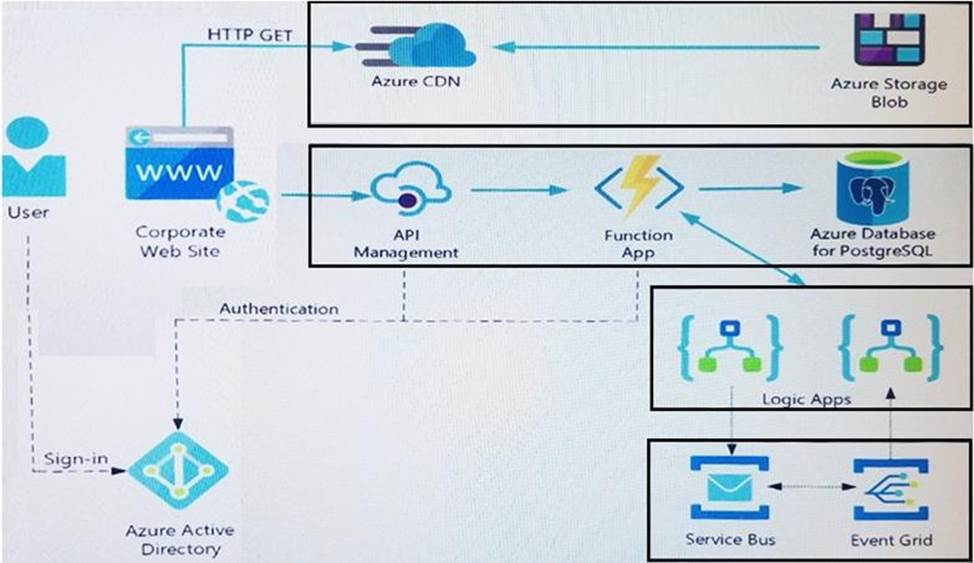
User authentication
The following steps detail the user authentication process:
✑ The user selects Sign in in the website.
✑ The browser redirects the user to the Azure Active Directory (Azure AD) sign in page.
✑ The user signs in.
✑ Azure AD redirects the user’s session back to the web application. The URL includes an access token.
✑ The web application calls an API and includes the access token in the authentication header. The application ID is sent as the audience (‘aud’) claim in the access token.
✑ The back-end API validates the access token.
Requirements
Corporate website
✑ Communications and content must be secured by using SSL.
✑ Communications must use HTTPS.
✑ Data must be replicated to a secondary region and three availability zones.
✑ Data storage costs must be minimized.
Azure Database for PostgreSQL
The database connection string is stored in Azure Key Vault with the following attributes:
✑ Azure Key Vault name: cpandlkeyvault
✑ Secret name: PostgreSQLConn
✑ Id: 80df3e46ffcd4f1cb187f79905e9a1e8
The connection information is updated frequently. The application must always use the latest information to connect to the database.
Azure Service Bus and Azure Event Grid
✑ Azure Event Grid must use Azure Service Bus for queue-based load leveling.
✑ Events in Azure Event Grid must be routed directly to Service Bus queues for use in buffering.
✑ Events from Azure Service Bus and other Azure services must continue to be routed to Azure Event Grid for processing.
Security
✑ All SSL certificates and credentials must be stored in Azure Key Vault.
✑ File access must restrict access by IP, protocol, and Azure AD rights.
✑ All user accounts and processes must receive only those privileges which are essential to perform their intended function.
Compliance
Auditing of the file updates and transfers must be enabled to comply with General Data Protection Regulation (GDPR). The file updates must be read-only, stored in the order in which they occurred, include only create, update, delete, and copy operations, and be retained for compliance reasons.
Issues
Corporate website
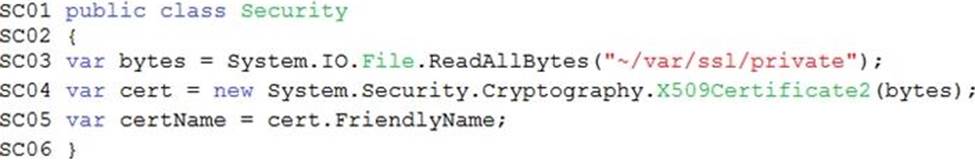
While testing the site, the following error message displays:
CryptographicException: The system cannot find the file specified.
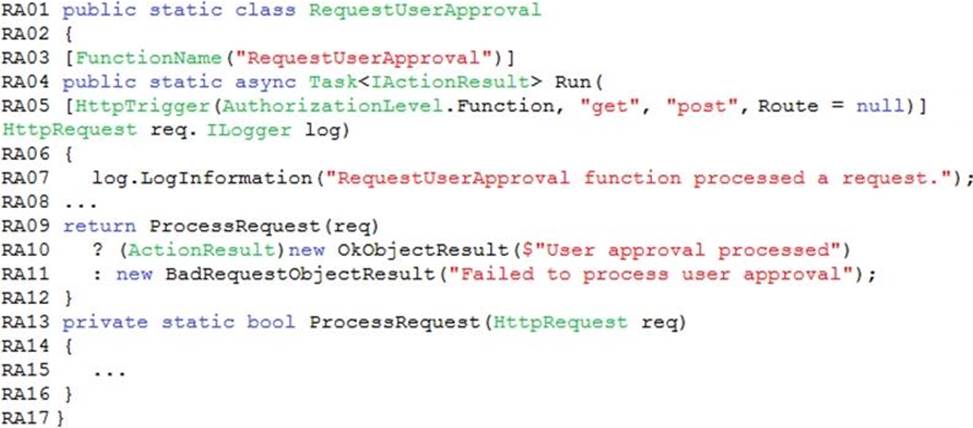
Function app
You perform local testing for the RequestUserApproval function. The following error
message displays:
‘Timeout value of 00:10:00 exceeded by function: RequestUserApproval’
The same error message displays when you test the function in an Azure development environment when you run the following Kusto query: FunctionAppLogs
| where FunctionName = = "RequestUserApproval"
Logic app
You test the Logic app in a development environment. The following error message displays:
‘400 Bad Request’
Troubleshooting of the error shows an HttpTrigger action to call the RequestUserApproval function.
Code
Corporate website
Security.cs:
Function app
RequestUserApproval.cs:
HOTSPOT
You need to configure security and compliance for the corporate website files.
Which Azure Blob storage settings should you use? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
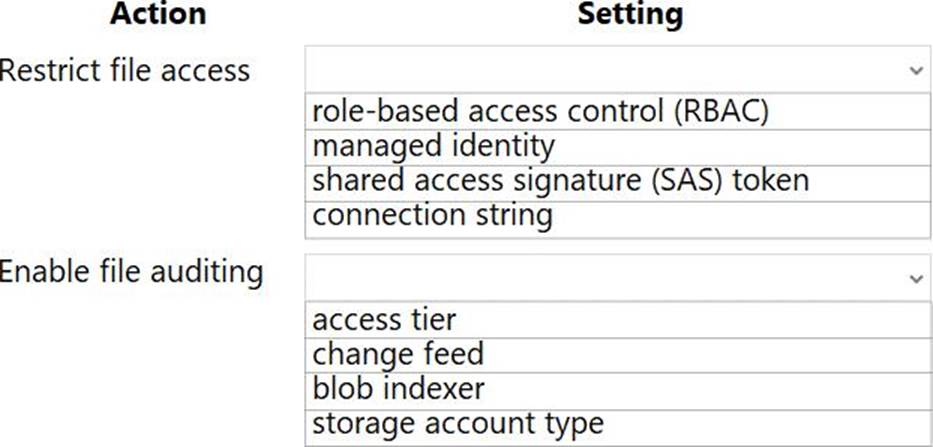
Answer: 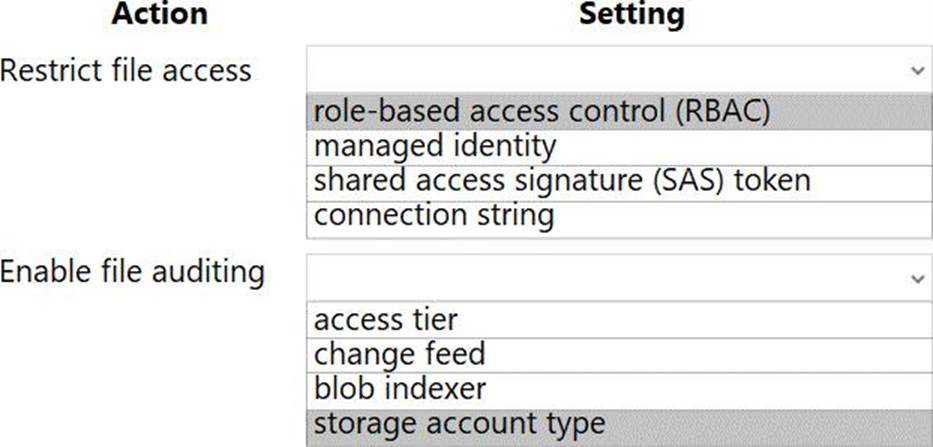
Explanation:
Box 1: role-based access control (RBAC)
Azure Storage supports authentication and authorization with Azure AD for the Blob and
Queue services via Azure role-based access control (Azure RBAC).
Scenario: File access must restrict access by IP, protocol, and Azure AD rights.
Box 2: change feed
The purpose of the change feed is to provide transaction logs of all the changes that occur to the blobs and the blob metadata in your storage account.
The file updates must be read-only, stored in the order in which they occurred, include only create, update, delete, and copy operations, and be retained for compliance reasons.
Latest AZ-204 Dumps Valid Version with 254 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

