What is the potential threat identified in this Stealthwatch dashboard?
Refer to the exhibit.
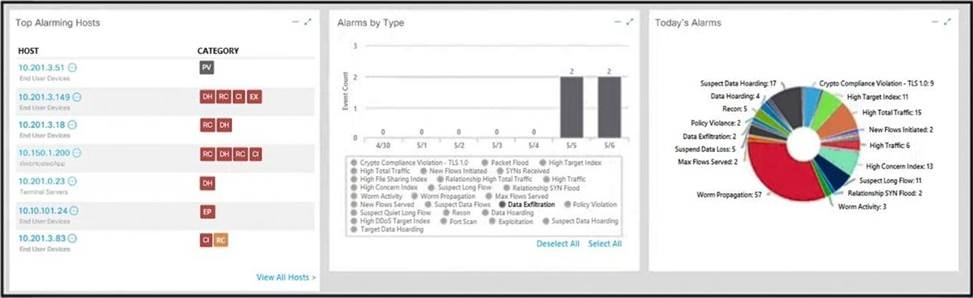
What is the potential threat identified in this Stealthwatch dashboard?
A . A policy violation is active for host 10.10.101.24.
B . A host on the network is sending a DDoS attack to another inside host.
C . There are two active data exfiltration alerts.
D . A policy violation is active for host 10.201.3.149.
Answer: C
Explanation:
The exhibit shows a Stealthwatch dashboard displaying information on alarming hosts, alarms by type, and today’s alarms. On the left side under “Top Alarming Hosts,” there are five host IP addresses listed with their respective categories indicating different types of alerts including ‘Data Hoarding’ and ‘Exfiltration.’ In “Alarms by Type” section at center top part of image shows bar graphs representing various alarm types including ‘Crypto Violation’ with their respective counts. On right side under “Today’s Alarms,” there’s a table showing the details of each alarm such as the host IP, the alarm type, the severity, and the time. The potential threat identified in this dashboard is that there are two active data exfiltration alerts, one for host 10.201.3.149 and another for host 10.10.101.24. Data exfiltration is the unauthorized transfer of data from a compromised system to an external destination, such as a command and control server or a malicious actor. This can result in data loss, breach of confidentiality, and damage to the organization’s reputation and assets.
Reference: = Cisco Cybersecurity Operations Fundamentals – Module 7: Network and Host Forensics
Latest 200-201 Dumps Valid Version with 154 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

