Symantec 250-441 Administration of Symantec Advanced Threat Protection 3.0 Online Training
Symantec 250-441 Online Training
The questions for 250-441 were last updated at Apr 13,2025.
- Exam Code: 250-441
- Exam Name: Administration of Symantec Advanced Threat Protection 3.0
- Certification Provider: Symantec
- Latest update: Apr 13,2025
How does an attacker use a zero-day vulnerability during the Incursion phase?
- A . To perform a SQL injection on an internal server
- B . To extract sensitive information from the target
- C . To perform network discovery on the target
- D . To deliver malicious code that breaches the target
Why is it important for an Incident Responder to review Related Incidents and Events when analyzing an incident for an After Actions Report?
- A . It ensures that the Incident is resolved, and the responder can clean up the infection.
- B . It ensures that the Incident is resolved, and the responder can determine the best remediation method.
- C . It ensures that the Incident is resolved, and the threat is NOT continuing to spread to other parts of the environment.
- D . It ensures that the Incident is resolved, and the responder can close out the incident in the ATP manager.
Which best practice does Symantec recommend with the Endpoint Detection and Response feature?
- A . Create a unique Cynic account to provide to ATP
- B . Create a unique Symantec Messaging Gateway account to provide to ATP
- C . Create a unique Symantec Protection Manager (SEPM) administrator account to provide to ATP
- D . Create a unique Email Security.cloud portal account to provide to ATP
What is the role of Cynic within the Advanced Threat Protection (ATP) solution?
- A . Reputation-based security
- B . Event correlation
- C . Network detection component
- D . Detonation/sandbox
Which section of the ATP console should an ATP Administrator use to create blacklists and whitelists?
- A . Reports
- B . Settings
- C . Action Manager
- D . Policies
How should an ATP Administrator configure Endpoint Detection and Response according to Symantec best practices for a SEP environment with more than one domain?
- A . Create a unique Symantec Endpoint Protection Manager (SEPM) domain for ATP
- B . Create an ATP manager for each Symantec Endpoint Protection Manager (SEPM) domain
- C . Create a Symantec Endpoint Protection Manager (SEPM) controller connection for each domain
- D . Create a Symantec Endpoint Protection Manager (SEPM) controller connection for the primary domain
Which attribute is required when configuring the Symantec Endpoint Protection Manager (SEPM) Log Collector?
- A . SEPM embedded database name
- B . SEPM embedded database type
- C . SEPM embedded database version
- D . SEPM embedded database password
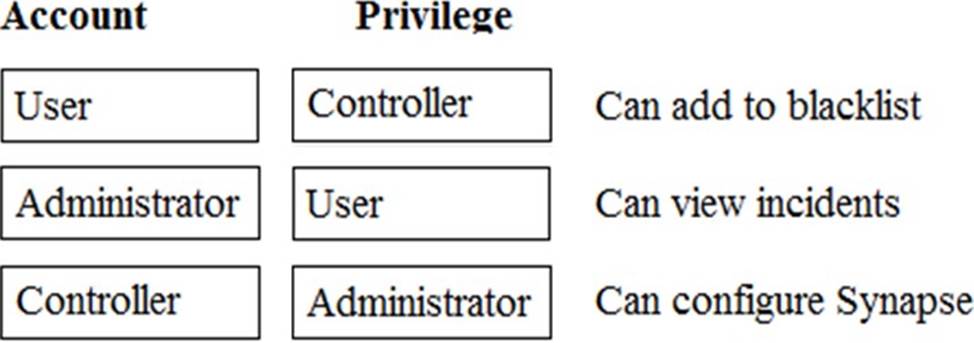
DRAG DROP
Which level of privilege corresponds to each ATP account type? Match the correct account type to the corresponding privileges.
An Incident Responder wants to run a database search that will list all client named starting with SYM.
Which syntax should the responder use?
- A . hostname like “SYM”
- B . hostname “SYM”
- C . hostname “SYM*”
- D . hostname like “SYM*”
What is the main constraint an ATP Administrator should consider when choosing a network scanner model?
- A . Throughput
- B . Bandwidth
- C . Link speed
- D . Number of users
Latest 250-441 Dumps Valid Version with 70 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund