Microsoft SC-300 Microsoft Identity and Access Administrator Online Training
Microsoft SC-300 Online Training
The questions for SC-300 were last updated at Feb 27,2026.
- Exam Code: SC-300
- Exam Name: Microsoft Identity and Access Administrator
- Certification Provider: Microsoft
- Latest update: Feb 27,2026
Topic 1, Litware, Inc
Overview
Litware, Inc. is a pharmaceutical company that has a subsidiary named fabrikam, inc Litware has offices in Boston and Seattle, but has employees located across the United States. Employees connect remotely to either office by using a VPN connection.
Identity Environment
The network contains an Active Directory forest named litware.com that is linked to an Azure Active Directory (Azure AD) tenant named litware.com. Azure AD Connect uses pass-through authentication and has password hash synchronization disabled. Litware.com contains a user named User1 who oversees all application development.
Litware implements Azure AD Application Proxy.
Fabrikam has an Azure AD tenant named fabrikam.com. The users at Fabrikam access the resources in litware.com by using guest accounts in the litware.com tenant.
Cloud Environment
All the users at Litware have Microsoft 365 Enterprise E5 licenses. All the built-in anomaly detection polices in Microsoft Cloud App Security are enabled.
Litware has an Azure subscription associated to the litware.com Azure AD tenant. The subscription contains an Azure Sentinel instance that uses the Azure Active Directory connector and the Office 365 connector. Azure Sentinel currently collects the Azure AD sign-ins logs and audit logs.
On-premises Environment
The on-premises network contains the severs shown in the following table.
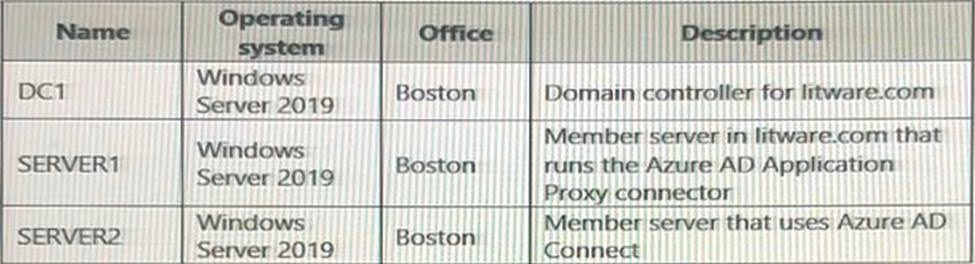
Both Litware offices connect directly to the internet. Both offices connect to virtual networks in the Azure subscription by using a site-to-site VPN connection. All on-premises domain controllers are prevented from accessing the internet.
Delegation Requirements
Litware identifies the following delegation requirements:
* Delegate the management of privileged roles by using Azure AD Privileged Identity Management (PIM).
* Prevent nonprivileged users from registering applications in the litware.com Azure AD tenant-
* Use custom catalogs and custom programs for Identity Governance.
* Ensure that User1 can create enterprise applications in Azure AD. Use the principle of least privilege.
Licensing Requirements
Litware recently added a custom user attribute named LWLicenses to the litware.com Active Directory forest. Litware wants to manage the assignment of Azure AD licenses by
modifying the value of the LWLicenses attribute. Users who have the appropriate value for LWLicenses must be added automatically to Microsoft 365 group that he appropriate license assigned.
Management Requirement
Litware wants to create a group named LWGroup1 will contain all the Azure AD user accounts for Litware but exclude all the Azure AD guest accounts.
Authentication Requirements
Litware identifies the following authentication requirements:
• Implement multi-factor authentication (MFA) for all Litware users.
• Exempt users from using MFA to authenticate to Azure AD from the Boston office of Litware.
• Implement a banned password list for the litware.com forest.
• Enforce MFA when accessing on-premises applications.
• Automatically detect and remediate externally leaked credentials
Access Requirements
Litware wants to create a group named LWGroup1 that will contain all the Azure AD user accounts for Litware but exclude all the Azure AD guest accounts.
Monitoring Requirements
Litware wants to use the Fusion rule in Azure Sentinel to detect multi-staged that include a combination of suspicious Azure AD sign-ins followed by anomalous Microsoft Office 365 activity.
You need to meet the authentication requirements for leaked credentials.
What should you do?
- A . Enable federation with PingFederate in Azure AD Connect.
- B . Configure Azure AD Password Protection.
- C . Enable password hash synchronization in Azure AD Connect.
- D . Configure an authentication method policy in Azure AD.
You need to configure the MFA settings for users who connect from the Boston office. The solution must meet the authentication requirements and the access requirements.
What should you configure?
- A . named locations that have a private IP address range
- B . named locations that have a public IP address range
- C . trusted IPs that have a public IP address range
- D . trusted IPs that have a private IP address range
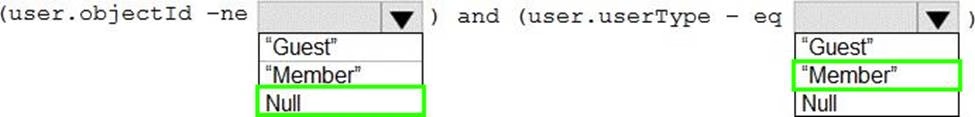
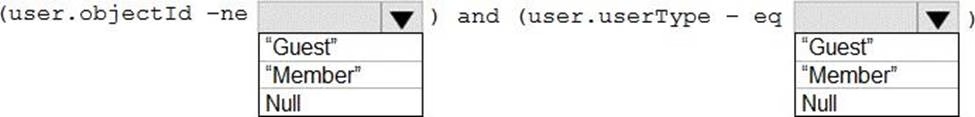
HOTSPOT
You need to create the LWGroup1 group to meet the management requirements.
How should you complete the dynamic membership rule? To answer, drag the appropriate values to the correct targets. Each value may be used once, more than once, or not at all. You many need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
You need to configure the detection of multi staged attacks to meet the monitoring requirements.
What should you do?
- A . Customize the Azure Sentinel rule logic.
- B . Create a workbook.
- C . Add an Azure Sentinel playbook.
- D . Add Azure Sentinel data connectors.
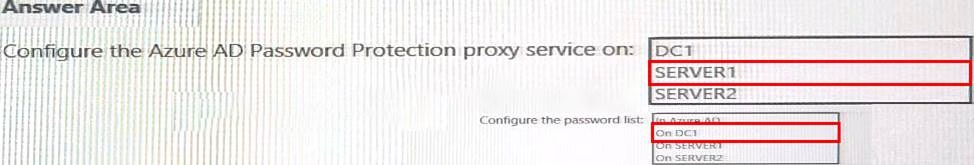
HOTSPOT
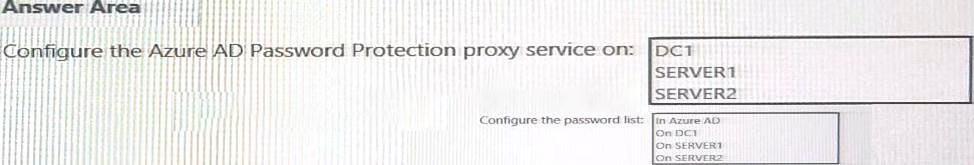
You need to implement password restrictions to meet the authentication requirements.
You install the Azure AD password Protection DC agent on DC1.
What should you do next? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
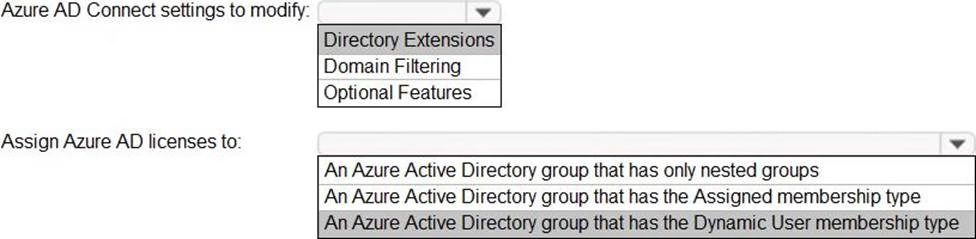
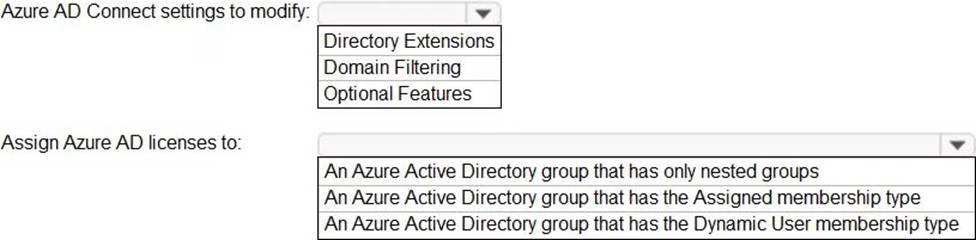
HOTSPOT
You need to configure the assignment of Azure AD licenses to the Litware users. The solution must meet the licensing requirements.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
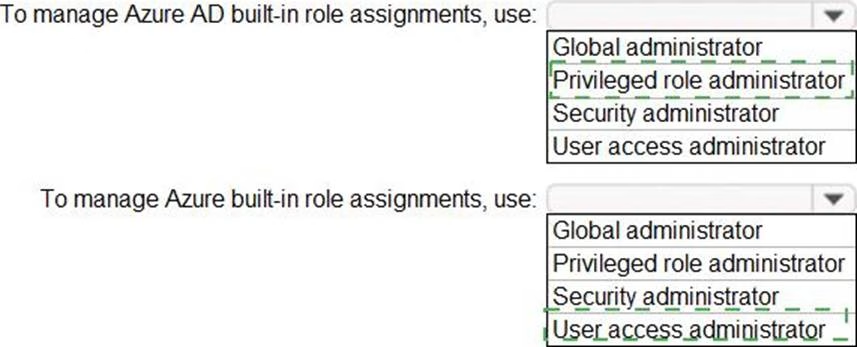
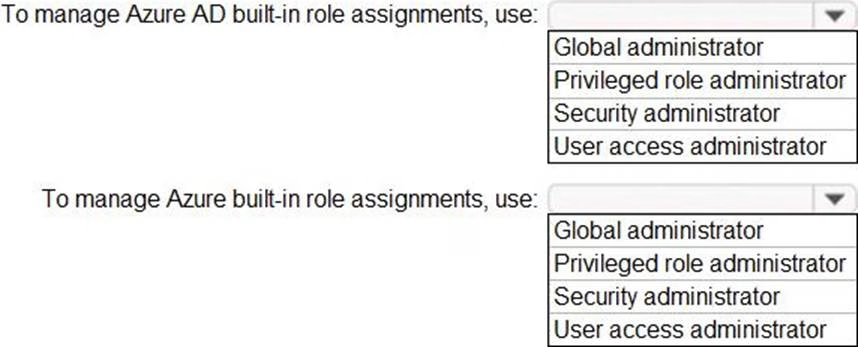
HOTSPOT
You need to identify which roles to use for managing role assignments. The solution must meet the delegation requirements.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
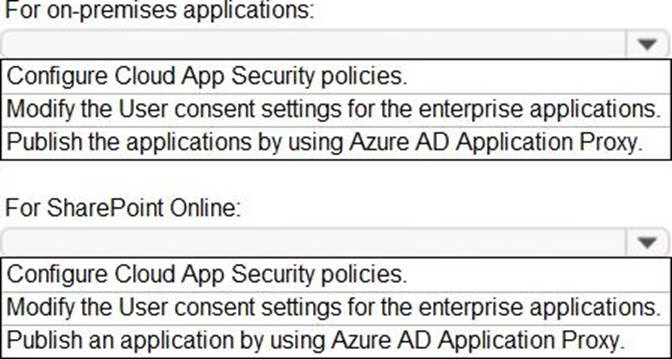
HOTSPOT
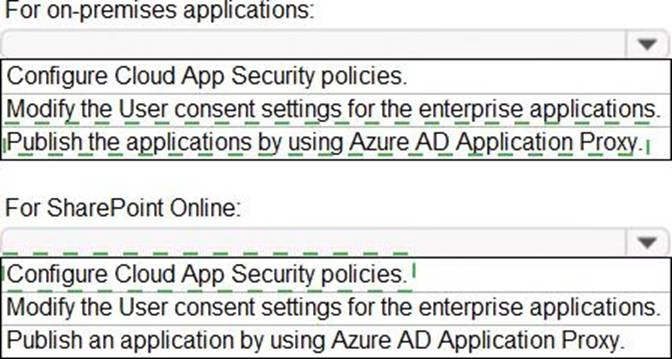
You need to implement on-premises application and SharePoint Online restrictions to meet the authentication requirements and the access requirements.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to configure the detection of multi-staged attacks to meet the monitoring requirements.
What should you do?
- A . Customize the Azure Sentinel rule logic.
- B . Create a workbook.
- C . Add Azure Sentinel data connectors.
- D . Add an Azure Sentinel playbook.
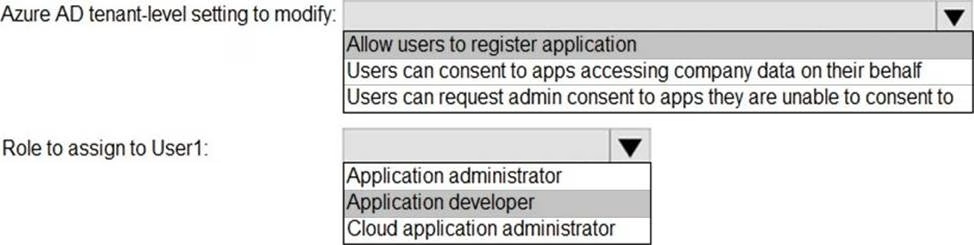
HOTSPOT
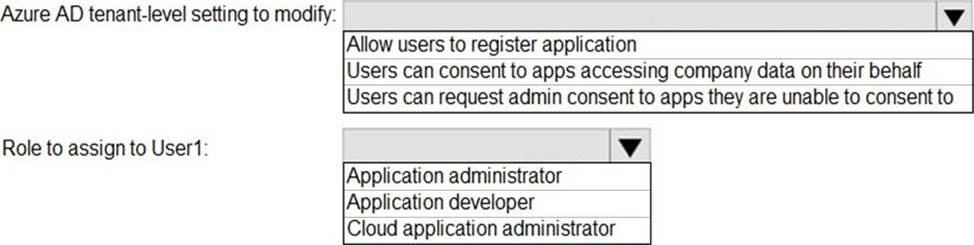
You need to configure app registration in Azure AD to meet the delegation requirements.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Latest SC-300 Dumps Valid Version with 106 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund