Microsoft SC-200 Microsoft Security Operations Analyst Online Training
Microsoft SC-200 Online Training
The questions for SC-200 were last updated at Feb 19,2026.
- Exam Code: SC-200
- Exam Name: Microsoft Security Operations Analyst
- Certification Provider: Microsoft
- Latest update: Feb 19,2026
HOTSPOT
You need to implement Microsoft Defender for Cloud to meet the Microsoft Defender for Cloud requirements and the business requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

Which rule setting should you configure to meet the Microsoft Sentinel requirements?
- A . From Set rule logic, turn off suppression.
- B . From Analytic rule details, configure the tactics.
- C . From Set rule logic, map the entities.
- D . From Analytic rule details, configure the severity.
You need to modify the anomaly detection policy settings to meet the Microsoft Defender for Cloud Apps requirements and resolve the reported problem.
Which policy should you modify?
- A . Activity from suspicious IP addresses
- B . Risky sign-in
- C . Activity from anonymous IP addresses
- D . Impossible travel
Topic 3, Adatum Corporation
Overview
Adatum Corporation is a United States-based financial services company that has regional offices in New York, Chicago, and San Francisco.
The on-premises network contains an Active Directory Domain Services (AD DS) forest named corp.adatum.com that syncs with an Azure AD tenant named adatum.com. All user and group management tasks are performed in corp.adatum.com. The corp.adatum.com domain contains a group named Group! that syncs with adatum.com.
All the users at Adatum are assigned a Microsoft 365 E5 license and an Azure Active Directory Perineum 92 license.
The cloud environment contains a Microsoft 365 subscription, an Azure subscription linked to the adatum.com tenant, and the resources shown in the following table.
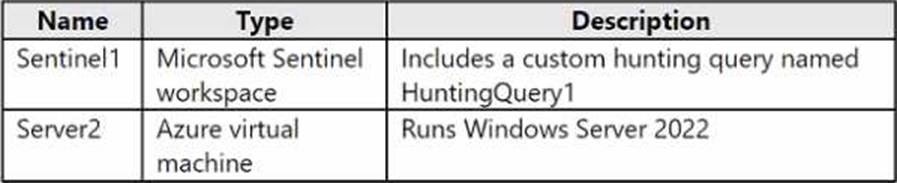
The on-premises network contains the resources shown in the following table.
Adatum plans to perform the following changes;
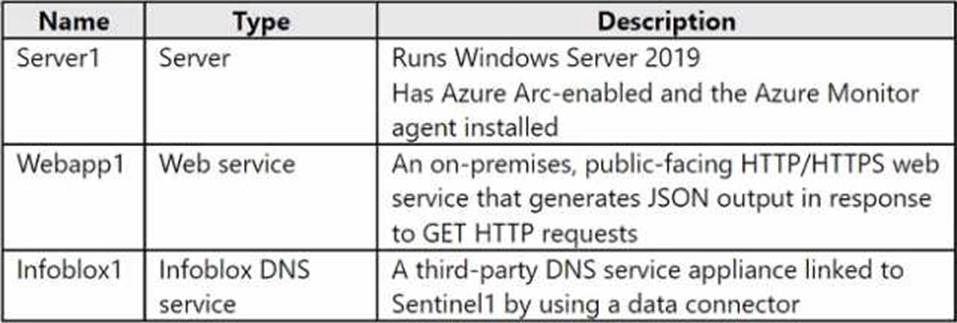
• Implement a query named rulequery1 that will include the following KQL query.
• Implement a Microsoft Sentinel scheduled rule that generates incidents based on rulequery1. Adatum identifies the following Microsoft Defender for Cloud requirements:
• The members of Group1 must be able to enable Defender for Cloud plans and apply regulatory compliance initiatives.
• Microsoft Defender for Servers Plan 2 must be enabled on all the Azure virtual machines.
• Server2 must be excluded from agentless scanning.
Adatum identifies the following Microsoft Sentinel requirements:
• Implement an Advanced Security Information Model (ASIM) query that will return a count of DNS requests that results in an NXDOMAIN response from Infoblox1.
• Ensure that multiple alerts generated by rulequery1 in response to a single user launching Azure Cloud Shell multiple times are consolidated as a single incident.
• Implement the Windows Security Events via AMA connector for Microsoft Sentinel and configure it to monitor the Security event log of Server1.
• Ensure that incidents generated by rulequery1 are closed automatically if Azure Cloud Shell is launched by the company’s SecOps team.
• Implement a custom Microsoft Sentinel workbook named Workbook1 that will include a query to dynamically retrieve data from Webapp1.
• Implement a Microsoft Sentinel near-real-time (NRT) analytics rule that detects sign-ins to a designated break glass account
• Ensure that HuntingQuery1 runs automatically when the Hunting page of Microsoft Sentinel in the Azure portal is accessed.
• Ensure that higher than normal volumes of password resets for corp.adatum.com user accounts are detected.
• Minimize the overhead associated with queries that use ASIM parsers.
• Ensure that the Group1 members can create and edit playbooks.
• Use built-in ASIM parsers whenever possible.
Adatum identifies the following business requirements:
• Follow the principle of least privilege whenever possible.
• Minimize administrative effort whenever possible. Directory Perineum 92 license.
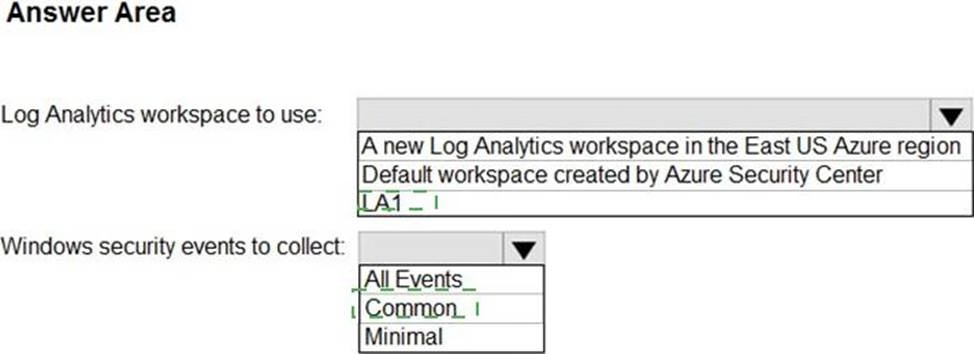
You need to configure event monitoring for Server1. The solution must meet the Microsoft Sentinel requirements.
What should you create first?
- A . a Microsoft Sentinel automation rule
- B . a Microsoft Sentinel scheduled query rule
- C . a Data Collection Rule (DCR)
- D . an Azure Event Grid topic
You need to implement the Defender for Cloud requirements.
What should you configure for Server2?
- A . the Microsoft Antimalware extension
- B . an Azure resource lock
- C . an Azure resource tag
- D . the Azure Automanage machine configuration extension for Windows
HOTSPOT
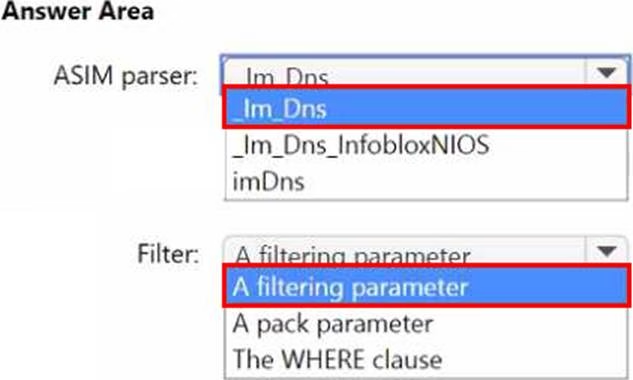
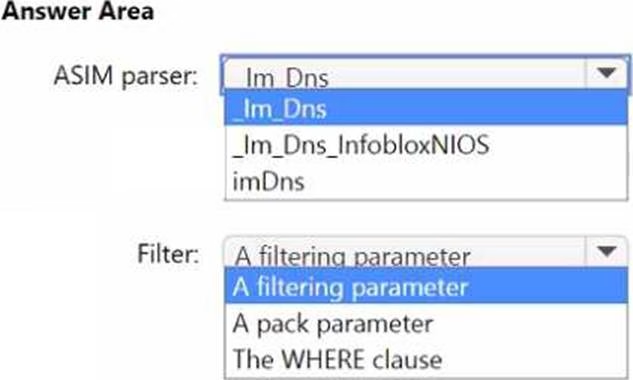
You need to implement the ASIM query for DNS requests. The solution must meet the Microsoft Sentinel requirements.
How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
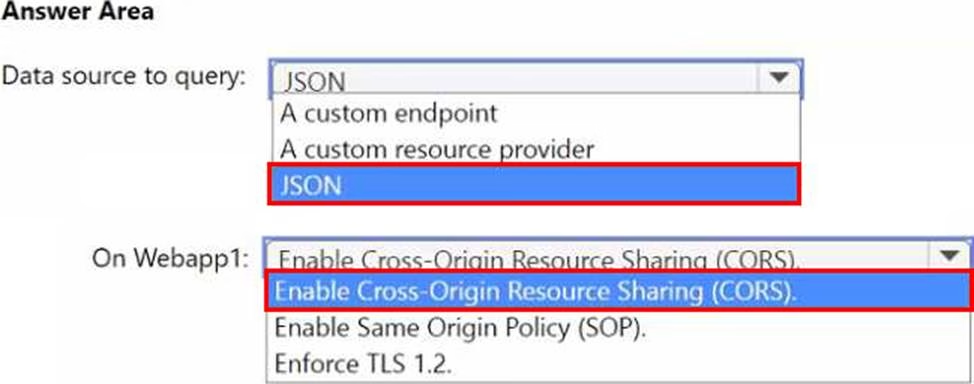
HOTSPOT
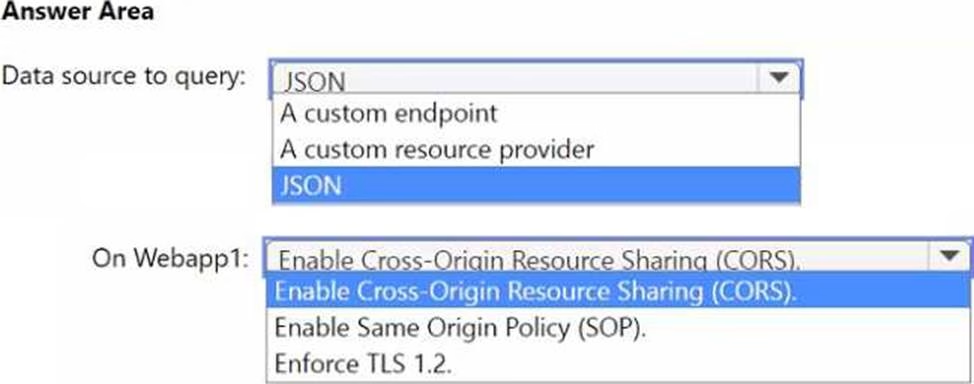
You need to implement the query for Workbook1 and Webapp1. The solution must meet the Microsoft Sentinel requirements.
How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to ensure that the configuration of HuntingQuery1 meets the Microsoft Sentinel requirements.
What should you do?
- A . Add HuntingQuery1 to a livestream.
- B . Create a watch list.
- C . Create an Azure Automation rule.
- D . Add HuntingQuery1 to favorites.
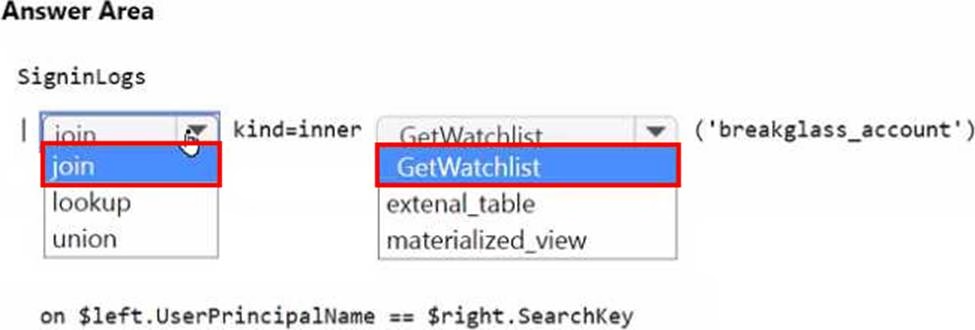
HOTSPOT
You need to implement the Microsoft Sentinel NRT rule for monitoring the designated break glass account. The solution must meet the Microsoft Sentinel requirements.
How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.

HOTSPOT
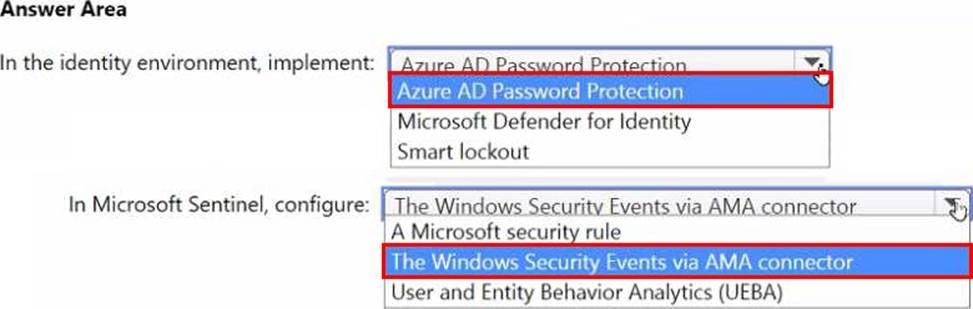
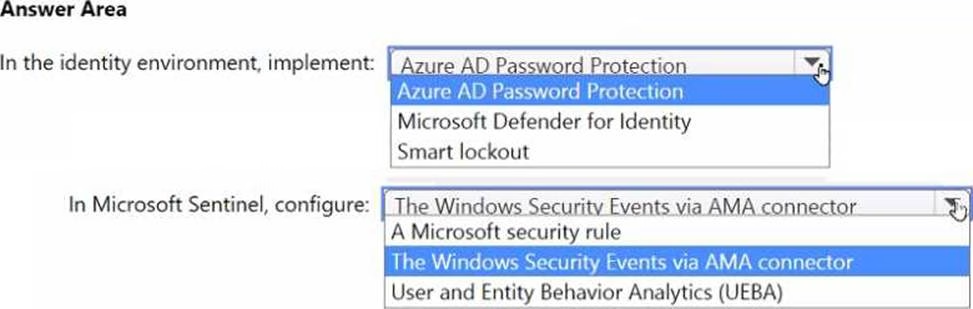
You need to monitor the password resets. The solution must meet the Microsoft Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Latest SC-200 Dumps Valid Version with 75 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund