Microsoft AZ-301 Microsoft Azure Architect Design Online Training
Microsoft AZ-301 Online Training
The questions for AZ-301 were last updated at Apr 03,2026.
- Exam Code: AZ-301
- Exam Name: Microsoft Azure Architect Design
- Certification Provider: Microsoft
- Latest update: Apr 03,2026
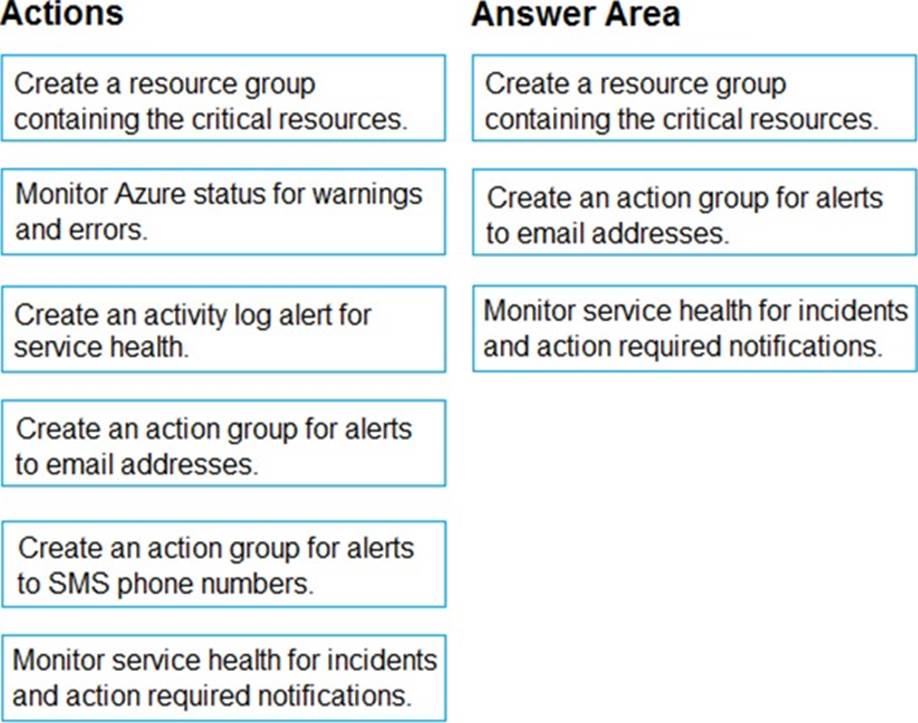
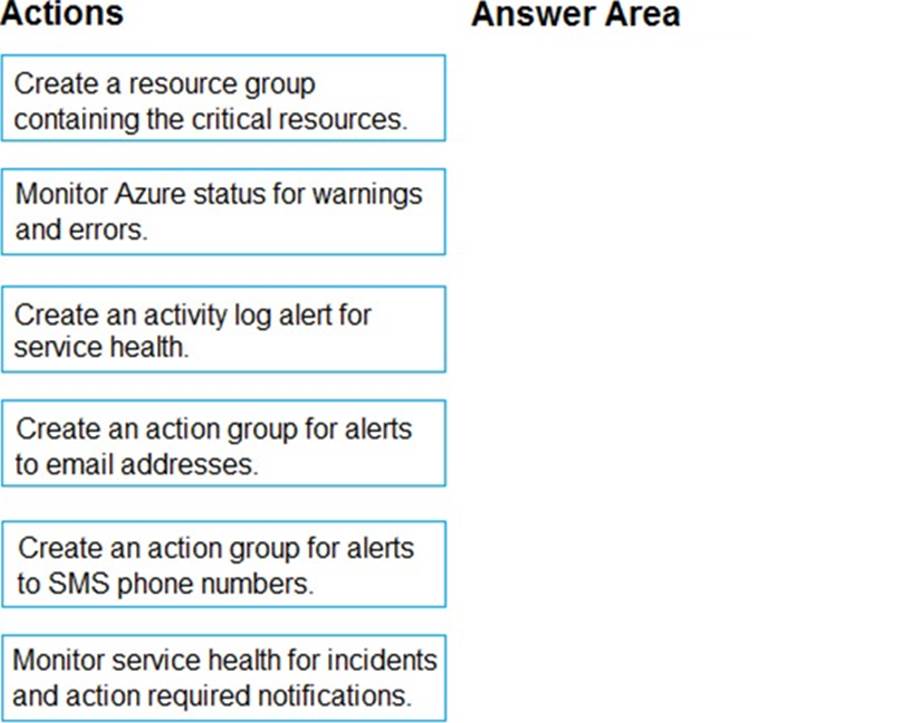
DRAG DROP
You plan to move several apps that handle critical line-of-business (LOB) services to Azure. Appropriate personnel must be notified if any critical resources become degraded or unavailable. You need to design a monitoring and notification strategy that can handle up to 100 notifications per hour.
Which three actions should you recommend be performed in sequence? To answer, move the appropriate
actions from the list of actions to the answer area and arrange them in the correct order. NOTE: More than one order of answer choices is correct. You will receive credit for any of the correct orders you select.
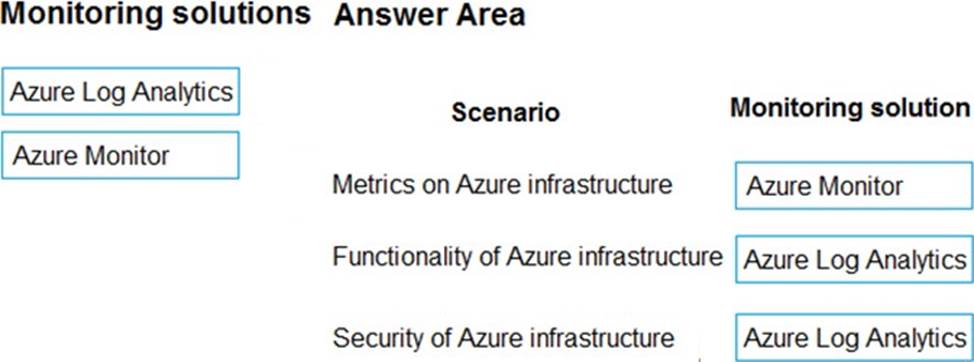
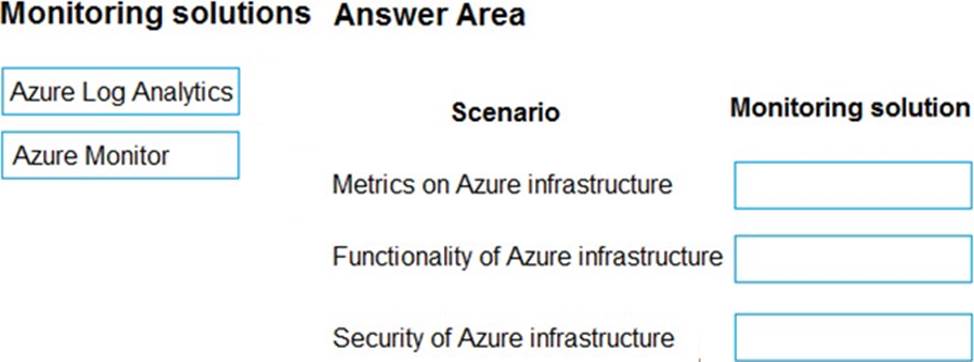
DRAG DROP
You manage a solution in Azure.
The solution is performing poorly.
You need to recommend tools to determine causes for the performance issues.
What should you recommend? To answer, drag the appropriate monitoring solutions to the correct scenarios. Each monitoring solution may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
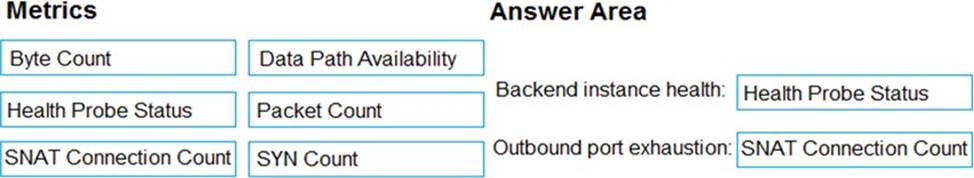
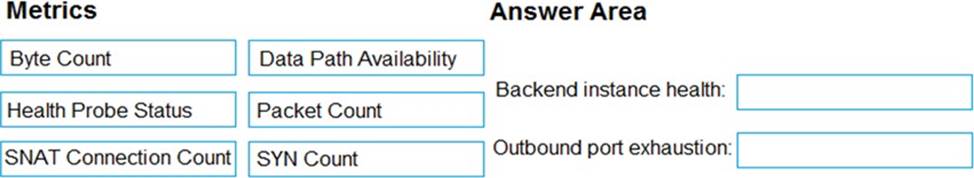
DRAG DROP
You have standard Load balancer configured to support three virtual machines on the same subnet. You need to recommend a solution to notify administrators when the load balancer fails.
Which metrics should you recommend using to test the load balancer? To answer, drag the appropriate metrics to the correct conditions. Each metric may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content. NOTE: Each correct selection is worth one point.
Please wait while the virtual machine loads. Once loaded, you may proceed to the lab section. This may take a few minutes, and the wait time will not be deducted from your overall test time.
When the Next button is available, click it to access the lad section. In this section, you will perform a set of tasks in a live environment. While most functionality will be available to you as it would be in a live environment, some functionality (e.g., copy and paste, ability to navigate to external websites) will not be possible by design.
Scoring is based on the outcome of performing the tasks stated in the lab. In other words, it doesn’t matter how you accomplish the task, if you successfully perform it, you will earn credit for that task.
Labs are not timed separately, and this exam may have more than one lab that you must complete. You can use as much time as you would like to complete each lab. But, you should manage your time appropriately to ensure that you are able to complete the lab(s) and all other sections of the exam in the time provided.
Please note that once you submit your work by clicking the Next button within a lab, you will NOT be able to return to the lab.
You may now click next to proceed to the lab.
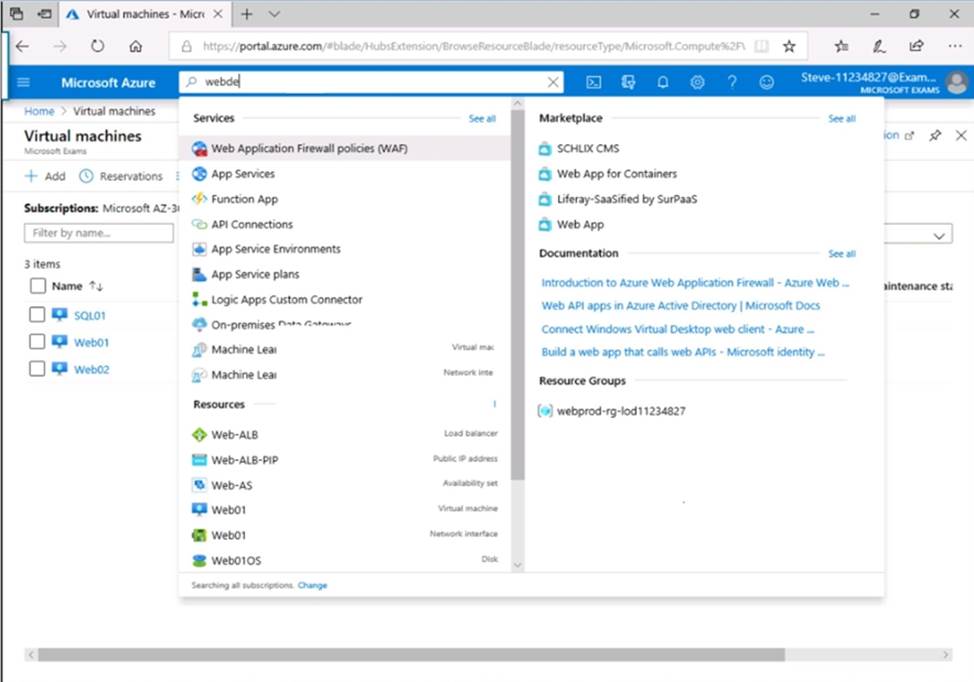
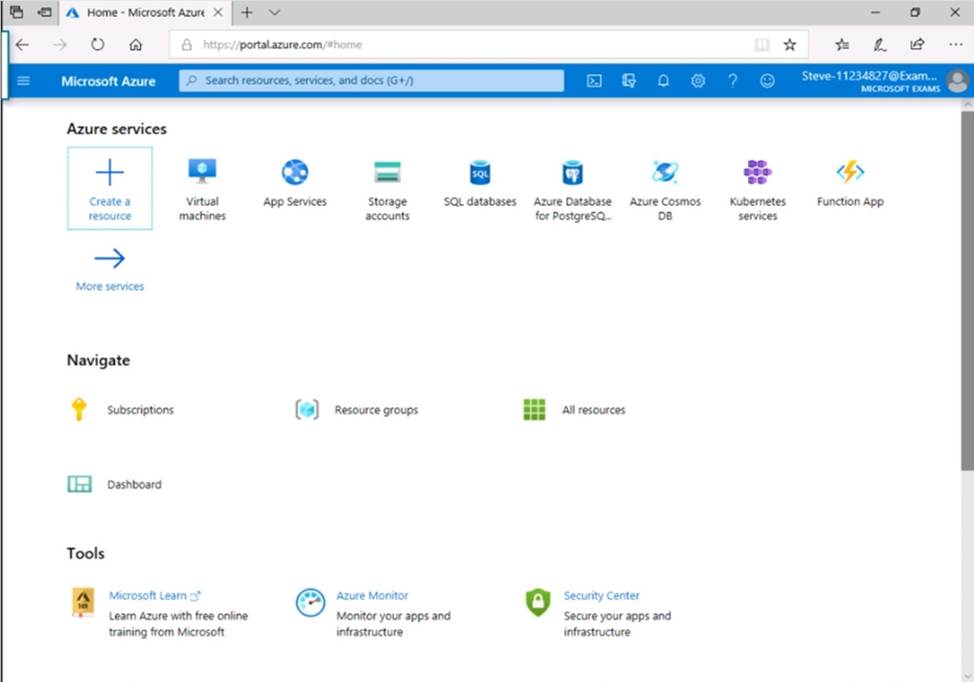
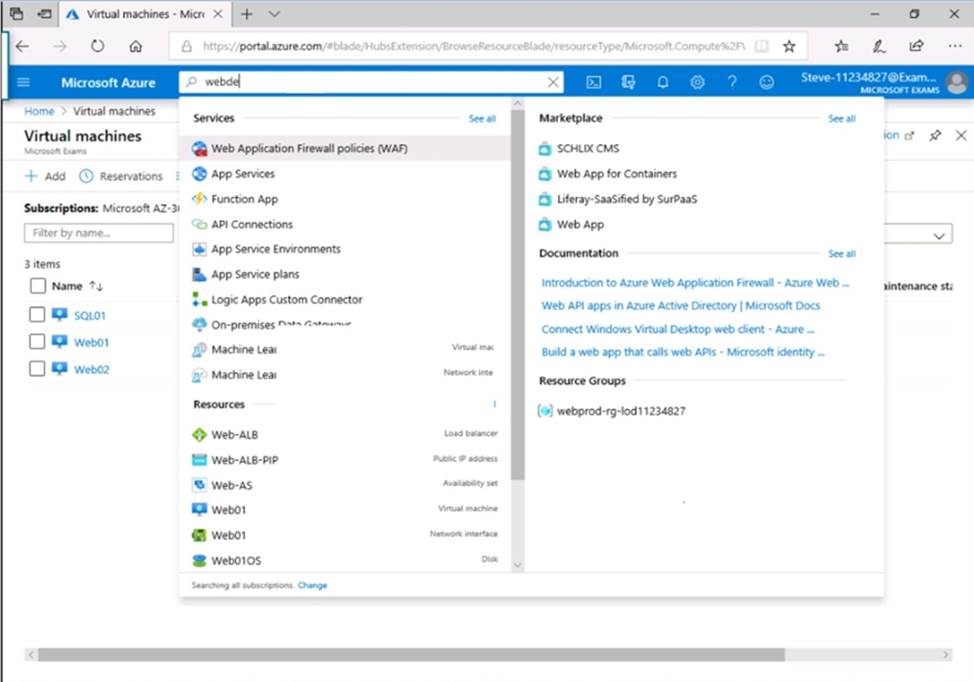
WebDev01 is used only for testing purposes.
You need to reduce the costs to host WebDev01.
What should you modify? NOTE: To answer this question, sign in to the Azure portal and explore the Azure resource groups.
- A . the disk type of WebDev01
- B . the networking properties of WebDev01
- C . the storage type of the storage account
- D . the properties of the storage account
Please wait while the virtual machine loads. Once loaded, you may proceed to the lab section. This may take a few minutes, and the wait time will not be deducted from your overall test time.
When the Next button is available, click it to access the lad section. In this section, you will perform a set of tasks in a live environment. While most functionality will be available to you as it would be in a live environment, some functionality (e.g., copy and paste, ability to navigate to external websites) will not be possible by design.
Scoring is based on the outcome of performing the tasks stated in the lab. In other words, it doesn’t matter how you accomplish the task, if you successfully perform it, you will earn credit for that task.
Labs are not timed separately, and this exam may have more than one lab that you must complete. You can use as much time as you would like to complete each lab. But, you should manage your time appropriately to ensure that you are able to complete the lab(s) and all other sections of the exam in the time provided.
Please note that once you submit your work by clicking the Next button within a lab, you will NOT be able to return to the lab.
You may now click next to proceed to the lab.
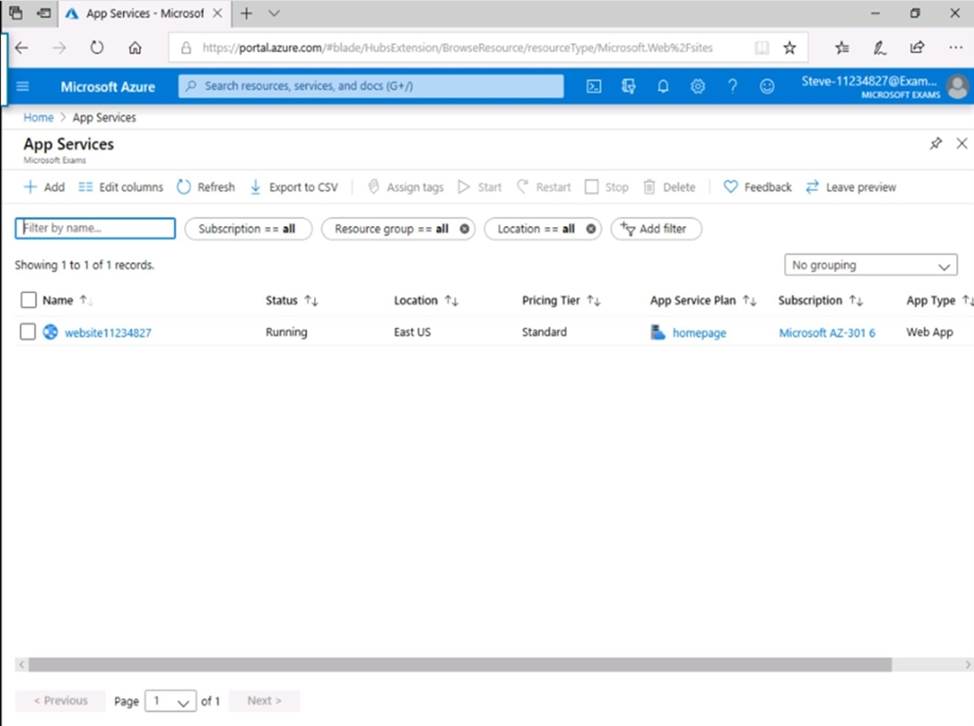
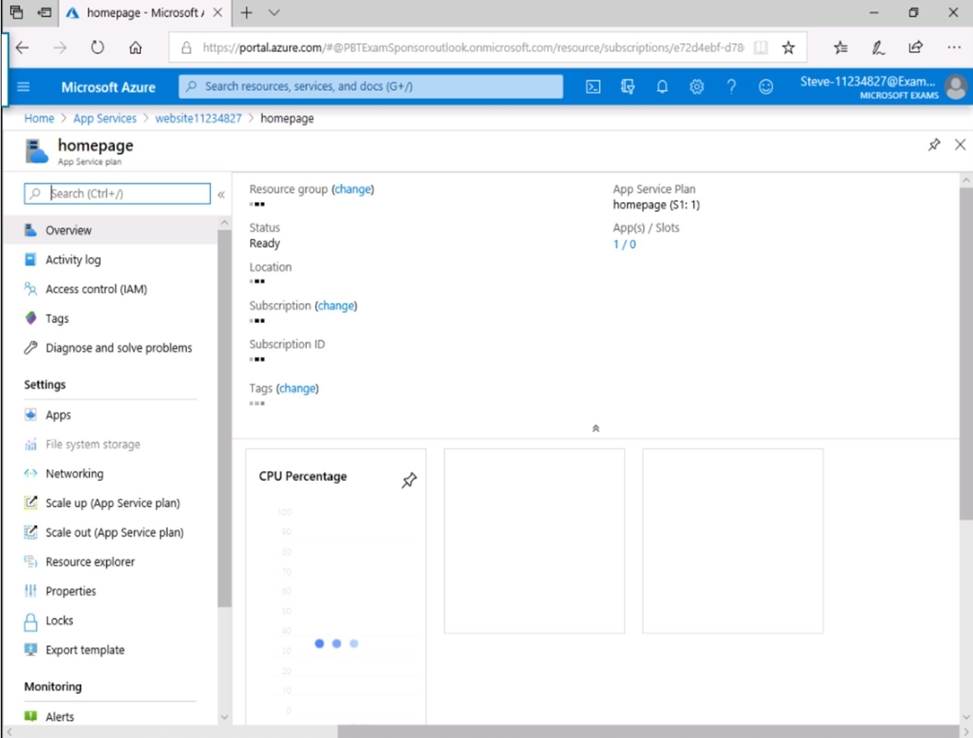
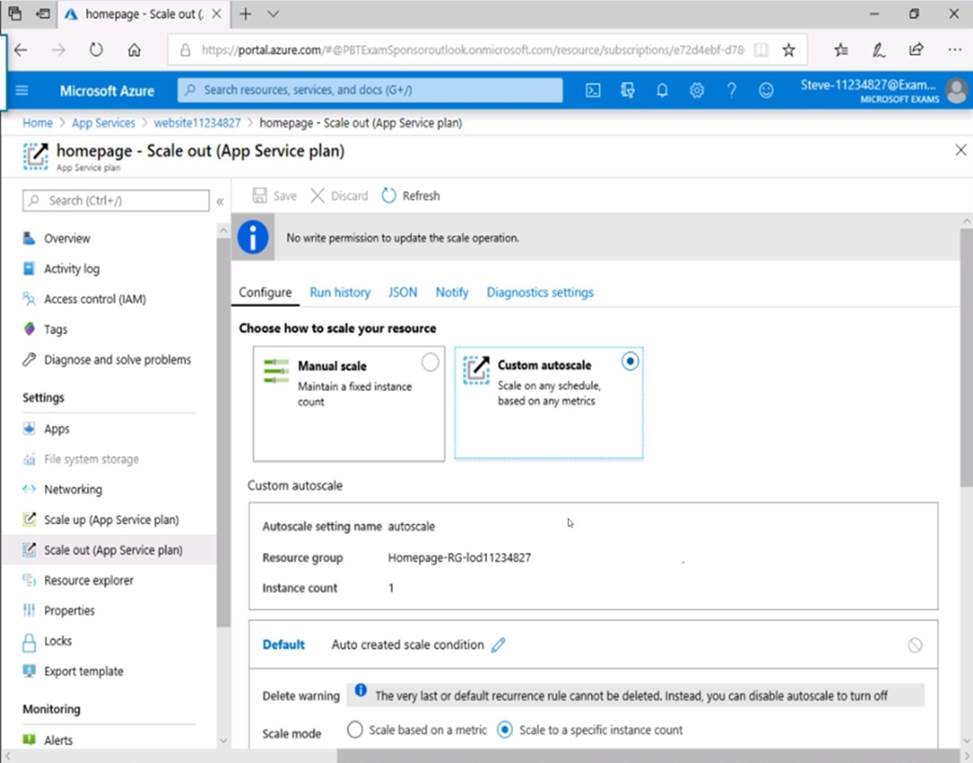
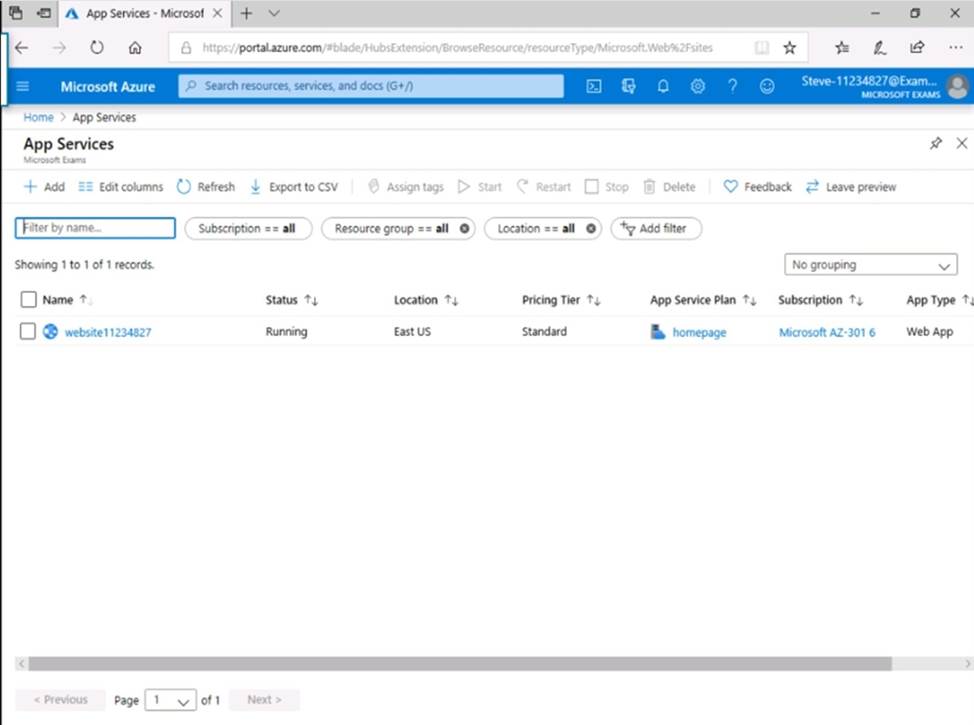
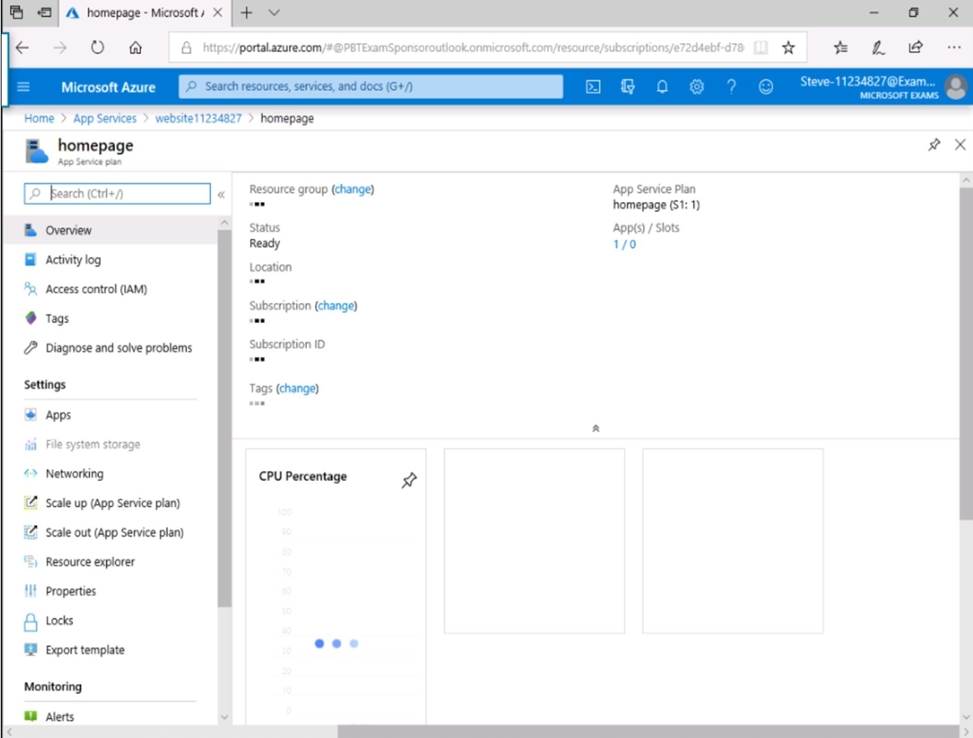
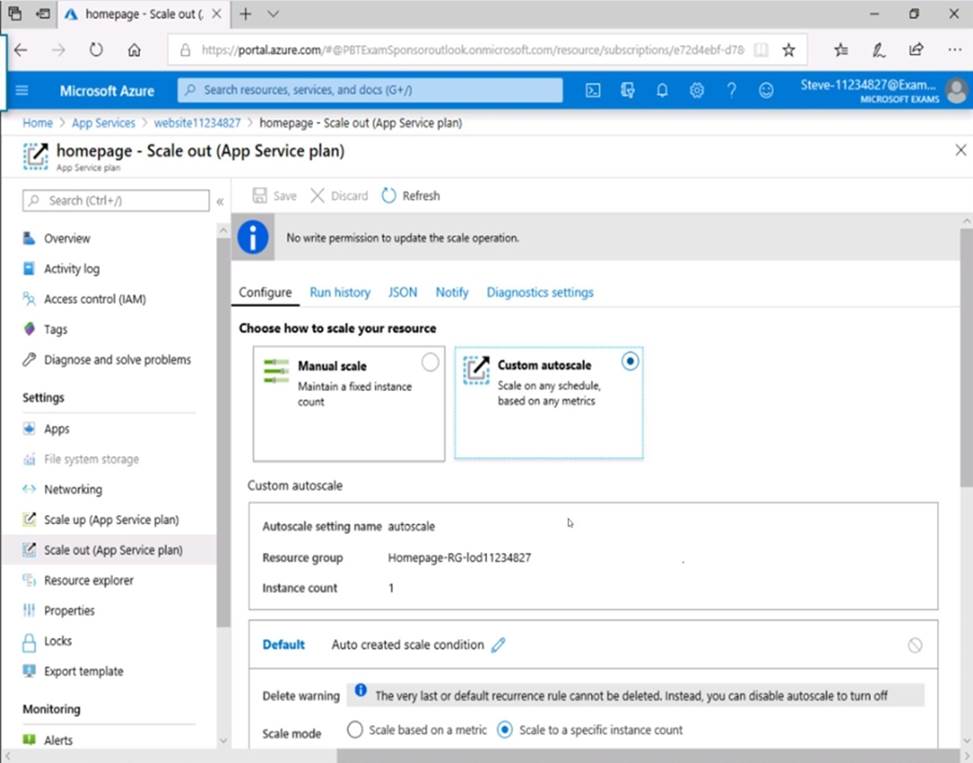
A user named [email protected] cannot modify the properties of the web app.
You need to ensure that [email protected] can modify the web app properties.
What should you do?
NOTE: To answer this question, sign in to the Azure portal and explore the Azure resource groups.
- A . Remove the resource lock from the resource group
- B . Remove the resource lock from the web app
- C . Modify the permissions on the web app
- D . Modify the permissions on the resource group
You are designing an Azure web app.
You need to ensure that users who have impaired vision can use the app.
Which reference material should you use when designing the app?
- A . Accessibility in Windows Dev Center
- B . Azure Application Architecture Guide
- C . Web Content Accessibility Guidelines
- D . Cloud Application Architecture Guide
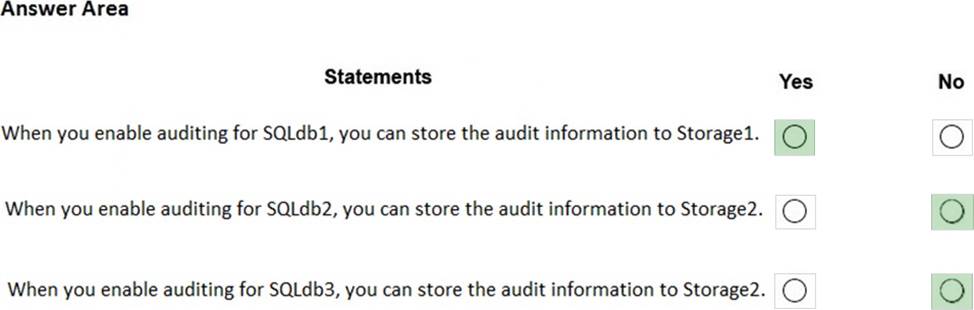
HOTSPOT
You have an Azure subscription that contains the Microsoft SQL servers shown in the following table.
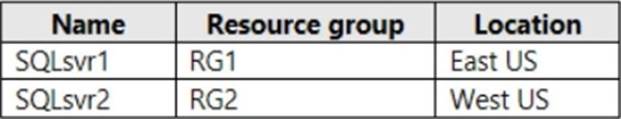
The subscription contains the storage accounts shown in the following table.
You create the Azure SQL databases shown in the following table.
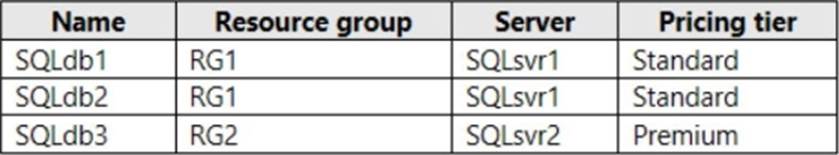
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
HOTSPOT
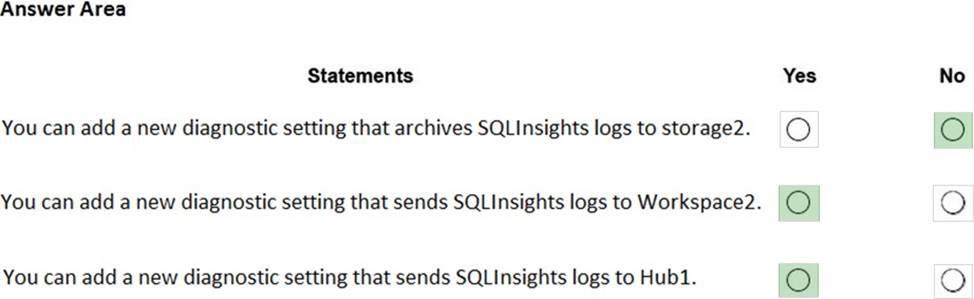
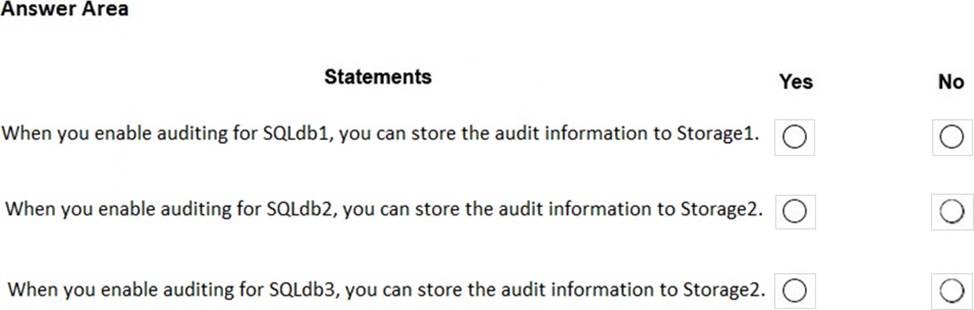
You have an Azure subscription that contains the resources shown in the following table.
You create an Azure SQL database named DB1 that is hosted in the East US region.
To DB1, you add a diagnostic setting named Settings1. Settings1 archives SQLInsights to storage1 and sends SQLInsights to Workspace1.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selections is worth one point.
Testlet 1
Case study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirement, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.
Overview
Contoso, Ltd. is a US-based financial services company that has a main office in New York and a branch office in San Francisco.
Existing Environment
Payment Processing System
Contoso hosts a business-critical payment processing system in its New York data center. The system has three tiers: a front-end web app, a middle-tier web API, and a back-end data store implemented as a Microsoft SQL Server 2014 database. All servers run Windows Server 2012 R2.
The front-end and middle-tier components are hosted by using Microsoft Internet Information Services (IIS). The application code is written in C# and ASP.NET. The middle-tier API uses the Entity Framework to communicate to the SQL Server database. Maintenance of the database is performed by using SQL Server Agent jobs.
The database is currently 2 TB and is not expected to grow beyond 3 TB.
The payment processing system has the following compliance-related requirements:
– Encrypt data in transit and at rest. Only the front-end and middle-tier components must be able to access the encryption keys that protect the data store.
– Keep backups of the data in two separate physical locations that are at least 200 miles apart and can be restored for up to seven years.
– Support blocking inbound and outbound traffic based on the source IP address, the destination IP address, and the port number.
– Collect Windows security logs from all the middle-tier servers and retain the logs for a period of seven years.
– Inspect inbound and outbound traffic from the front-end tier by using highly available network appliances.
– Only allow all access to all the tiers from the internal network of Contoso.
Tape backups are configured by using an on-premises deployment of Microsoft System Center Data Protection Manager (DPM), and then shipped offsite for long term storage.
Historical Transaction Query System
Contoso recently migrated a business-critical workload to Azure. The workload contains a .NET web service for querying the historical transaction data residing in Azure Table Storage. The .NET web service is accessible from a client app that was developed in-house and runs on the client computers in the New York office. The data in the table storage is 50 GB and is not expected to increase.
Current Issues
The Contoso IT team discovers poor performance of the historical transaction query system, at the queries frequently cause table scans.
Requirements
Planned Changes
Contoso plans to implement the following changes:
– Migrate the payment processing system to Azure.
– Migrate the historical transaction data to Azure Cosmos DB to address the performance issues.
Migration Requirements
Contoso identifies the following general migration requirements:
– Infrastructure services must remain available if a region or a data center fails. Failover must occur without any administrative intervention.
– Whenever possible, Azure managed services must be used to minimize management overhead.
– Whenever possible, costs must be minimized.
Contoso identifies the following requirements for the payment processing system:
– If a data center fails, ensure that the payment processing system remains available without any administrative intervention. The middle-tier and the web front end must continue to operate without any additional configurations.
– Ensure that the number of compute nodes of the front-end and the middle tiers of the payment processing system can increase or decrease automatically based on CPU utilization.
– Ensure that each tier of the payment processing system is subject to a Service Level Agreement (SLA) of 99.99 percent availability.
– Minimize the effort required to modify the middle-tier API and the back-end tier of the payment processing system.
– Generate alerts when unauthorized login attempts occur on the middle-tier virtual machines.
– Ensure that the payment processing system preserves its current compliance status.
– Host the middle tier of the payment processing system on a virtual machine.
Contoso identifies the following requirements for the historical transaction query system:
– Minimize the use of on-premises infrastructure services.
– Minimize the effort required to modify the .NET web service querying Azure Cosmos DB.
– Minimize the frequency of table scans.
– If a region fails, ensure that the historical transaction query system remains available without any administrative intervention.
Information Security Requirements
The IT security team wants to ensure that identity management is performed by using Active Directory. Password hashes must be stored on-premises only.
Access to all business-critical systems must rely on Active Directory credentials. Any suspicious authentication attempts must trigger a multi-factor authentication prompt automatically. legitimate users must be able to authenticate successfully by using multi-factor authentication.
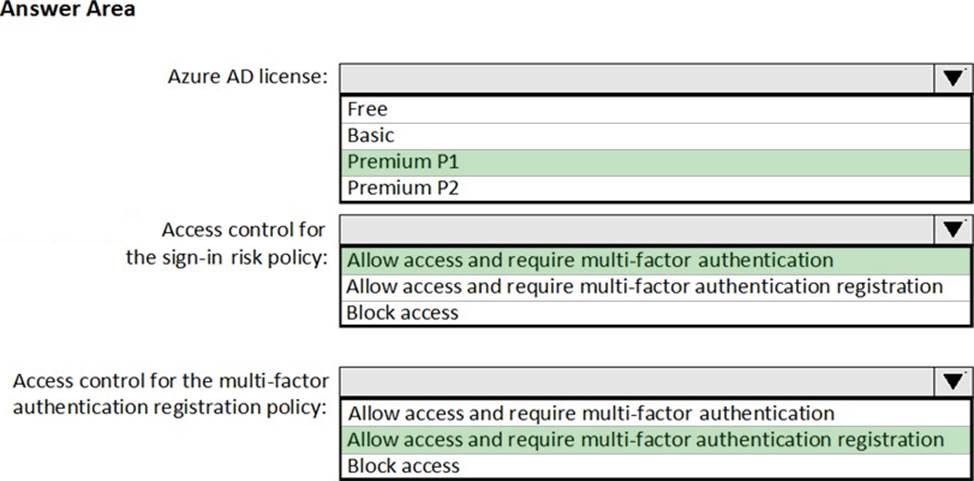
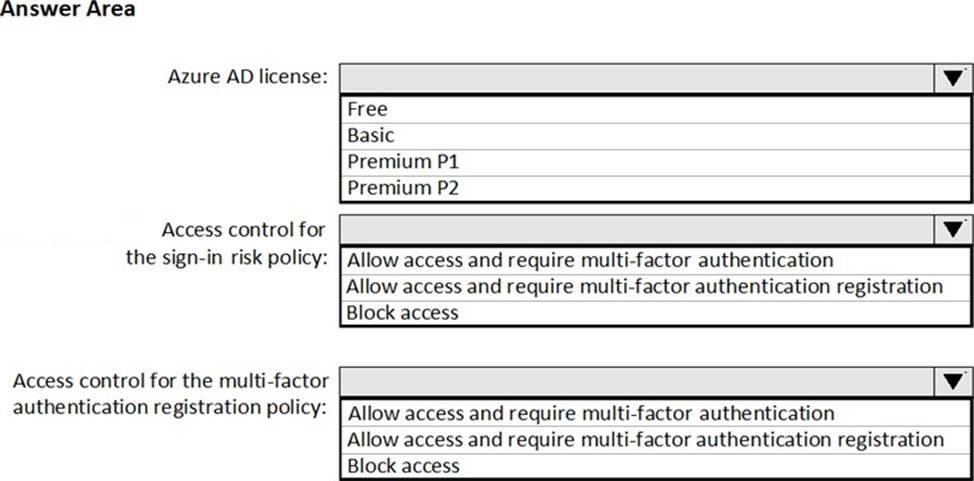
HOTSPOT
You need to recommend a solution for configuring the Azure Multi-Factor Authentication (MFA) settings.
What should you include in the recommendation? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
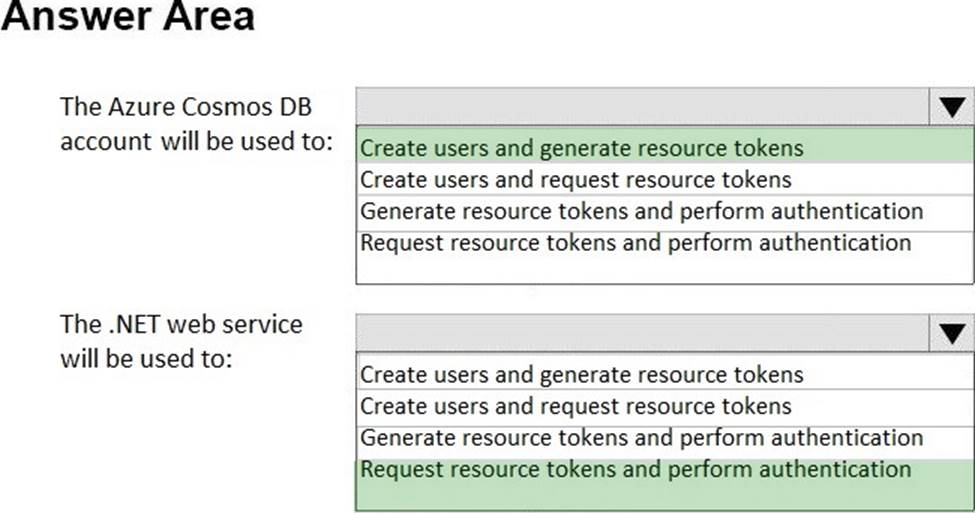
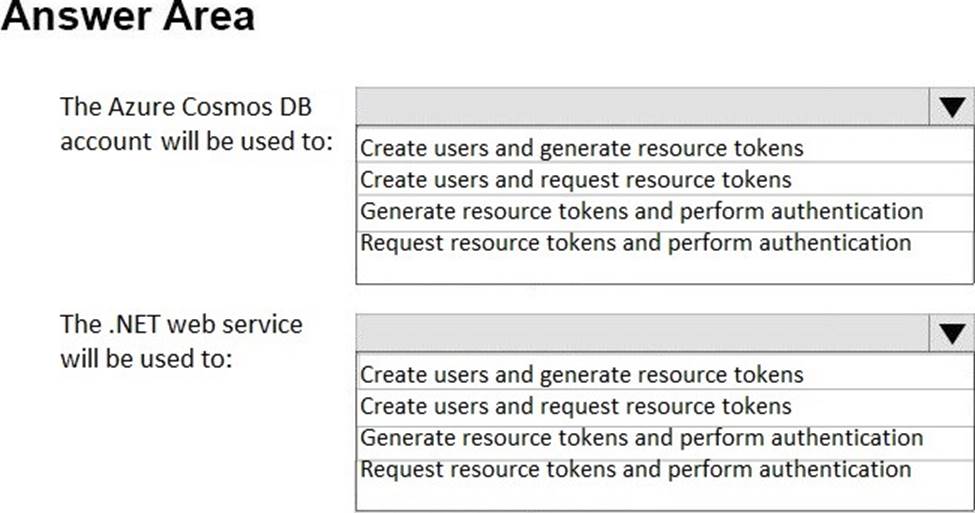
HOTSPOT
You need to design a solution for securing access to the historical transaction data.
What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Latest AZ-301 Dumps Valid Version with 293 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund