GIAC GCCC GIAC Critical Controls Certification (GCCC) Online Training
GIAC GCCC Online Training
The questions for GCCC were last updated at Mar 03,2026.
- Exam Code: GCCC
- Exam Name: GIAC Critical Controls Certification (GCCC)
- Certification Provider: GIAC
- Latest update: Mar 03,2026
A security incident investigation identified the following modified version of a legitimate system file on a compromised client:
C:WindowsSystem32winxml.dll Addition Jan. 16, 2014 4:53:11 PM
The infection vector was determined to be a vulnerable browser plug-in installed by the user.
Which of the organization’s CIS Controls failed?
- A . Application Software Security
- B . Inventory and Control of Software Assets
- C . Maintenance, Monitoring, and Analysis of Audit Logs
- D . Inventory and Control of Hardware Assets
What type of Unified Modelling Language (UML) diagram is used to show dependencies between logical groupings in a system?
- A . Package diagram
- B . Deployment diagram
- C . Class diagram
- D . Use case diagram
An organization is implementing a control within the Application Software Security CIS Control.
How can they best protect against injection attacks against their custom web application and database applications?
- A . Ensure the web application server logs are going to a central log host
- B . Filter input to only allow safe characters and strings
- C . Configure the web server to use Unicode characters only
- D . Check user input against a list of reserved database terms
What is a recommended defense for the CIS Control for Application Software Security?
- A . Keep debugging code in production web applications for quick troubleshooting
- B . Limit access to the web application production environment to just the developers
- C . Run a dedicated vulnerability scanner against backend databases
- D . Display system error messages for only non-kernel related events
A need has been identified to organize and control access to different classifications of
information stored on a fileserver.
Which of the following approaches will meet this need?
- A . Organize files according to the user that created them and allow the user to determine permissions
- B . Divide the documents into confidential, internal, and public folders, and ser permissions on each folder
- C . Set user roles by job or position, and create permission by role for each file
- D . Divide the documents by department and set permissions on each departmental folder
Below is a screenshot from a deployed next-generation firewall.
These configuration settings would be a defensive measure for which CIS Control?
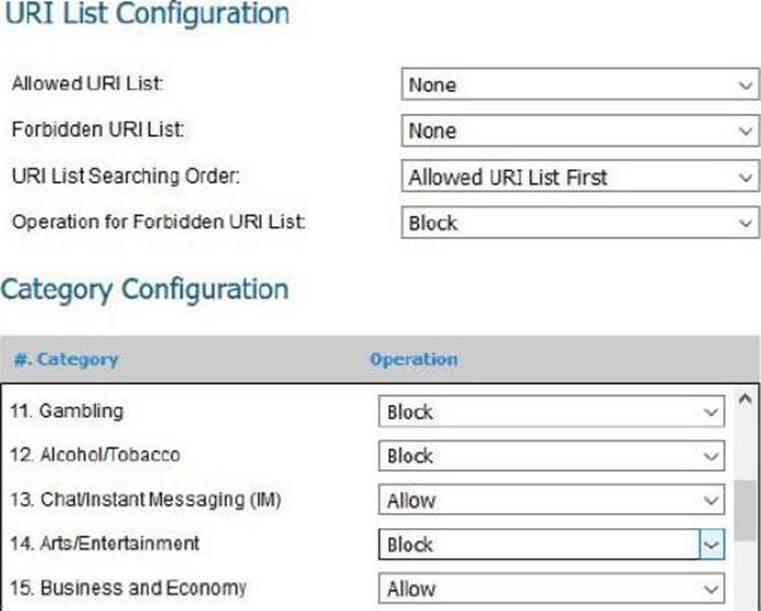
- A . Controlled Access Based on the Need to Know
- B . Limitation and Control of Network Ports, Protocols and Services
- C . Email and Web Browser Protections
- D . Secure Configuration for Network Devices, such as Firewalls, Routers and Switches.
Based on the data shown below.
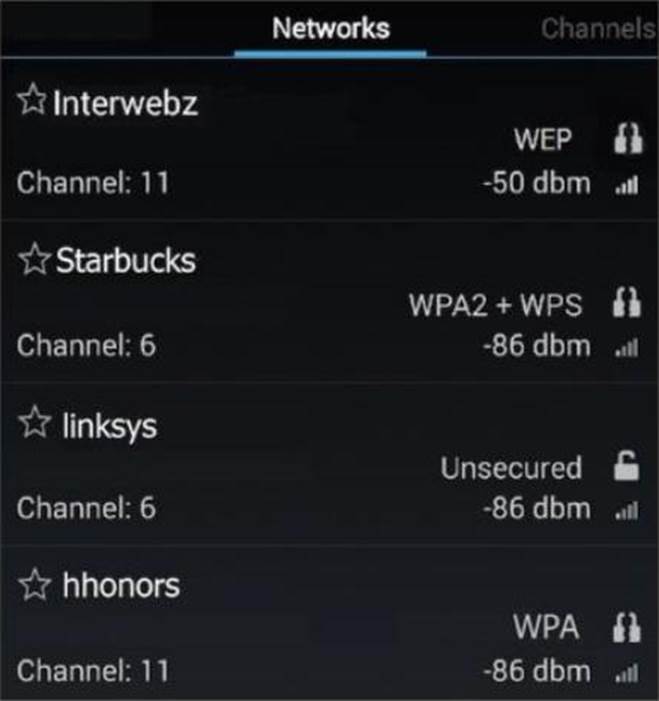
Which wireless access point has the manufacturer default settings still in place?
- A . Starbucks
- B . Linksys
- C . Hhonors
- D . Interwebz
Which of the following should be used to test antivirus software?
- A . FIPS 140-2
- B . Code Red
- C . Heartbleed
- D . EICAR
Which of the following best describes the CIS Controls?
- A . Technical, administrative, and policy controls based on research provided by the SANS Institute
- B . Technical controls designed to provide protection from the most damaging attacks based on current threat data
- C . Technical controls designed to augment the NIST 800 series
- D . Technical, administrative, and policy controls based on current regulations and security best practices
An attacker is able to successfully access a web application as root using ‘ or 1 = 1 . as the password. The successful access indicates a failure of what process?
- A . Input Validation
- B . Output Sanitization
- C . URL Encoding
- D . Account Management
Latest GCCC Dumps Valid Version with 93 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

