GIAC GCCC GIAC Critical Controls Certification (GCCC) Online Training
GIAC GCCC Online Training
The questions for GCCC were last updated at Mar 02,2026.
- Exam Code: GCCC
- Exam Name: GIAC Critical Controls Certification (GCCC)
- Certification Provider: GIAC
- Latest update: Mar 02,2026
Dragonfly Industries requires firewall rules to go through a change management system before they are configured. Review the change management log.
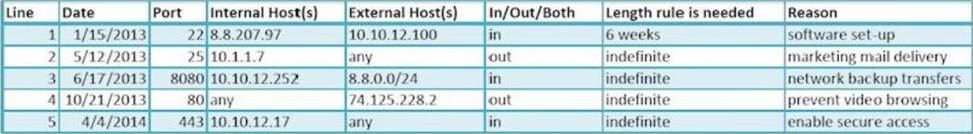
Which of the following lines in your firewall ruleset has expired and should be removed from the configuration?
- A . access-list outbound permit tcp host 10.1.1.7 any eq smtp
- B . access-list outbound deny tcp any host 74.125.228.2 eq www
- C . access-list inbound permit tcp 8.8.0.0 0.0.0.255 10.10.12.252 eq 8080
- D . access-list inbound permit tcp host 8.8.207.97 host 10.10.12.100 eq ssh
Which of the following actions produced the output seen below?
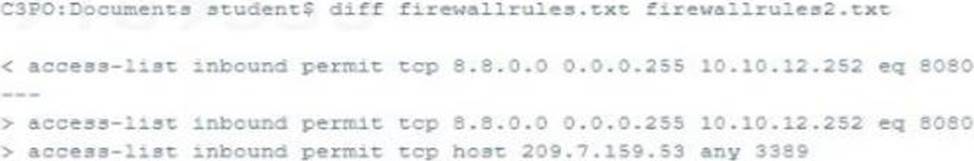
- A . An access rule was removed from firewallrules.txt
- B . An access rule was added to firewallrules2.txt
- C . An access rule was added to firewallrules.txt
- D . An access rule was removed from firewallrules2.txt
An organization has implemented a policy to detect and remove malicious software from its network.
Which of the following actions is focused on correcting rather than preventing attack?
- A . Configuring a firewall to only allow communication to whitelisted hosts and ports
- B . Using Network access control to disable communication by hosts with viruses
- C . Disabling autorun features on all workstations on the network
- D . Training users to recognize potential phishing attempts
An Internet retailer’s database was recently exploited by a foreign criminal organization via a remote attack. The initial exploit resulted in immediate root-level access.
What could have been done to prevent this level of access being given to the intruder upon successful exploitation?
- A . Configure the DMZ firewall to block unnecessary service
- B . Install host integrity monitoring software
- C . Install updated anti-virus software
- D . Configure the database to run with lower privileges
As part of an effort to implement a control on E-mail and Web Protections, an organization is monitoring their webserver traffic.
Which event should they receive an alert on?
- A . The number of website hits is higher that the daily average
- B . The logfiles of the webserver are rotated and archived
- C . The website does not respond to a SYN packet for 30 minutes
- D . The website issues a RST to a client after the connection is idle
Implementing which of the following will decrease spoofed e-mail messages?
- A . Finger Protocol
- B . Sender Policy Framework
- C . Network Address Translation
- D . Internet Message Access Protocol
After installing a software package on several workstations, an administrator discovered the software opened network port TCP 23456 on each workstation. The port is part of a software management function that is not needed on corporate workstations.
Which actions would best protect the computers with the software package installed?
- A . Document the port number and request approval from a change control group
- B . Redirect traffic to and from the software management port to a non-default port
- C . Block TCP 23456 at the network perimeter firewall
- D . Determine which service controls the software management function and opens the port, and disable it
Given the audit finding below, which CIS Control was being measured?
![]()
- A . Controlled Access Based on the Need to Know
- B . Controlled Use of Administrative Privilege
- C . Limitation and Control of Network Ports, Protocols and Services
- D . Secure Configurations for Hardware and Software on Laptops, Workstations, and Servers
- E . Inventory and Control of Hardware Assets
According to attack lifecycle models, what is the attacker’s first step in compromising an organization?
- A . Privilege Escalation
- B . Exploitation
- C . Initial Compromise
- D . Reconnaissance
Which of the following items would be used reactively for incident response?
- A . A schedule for creating and storing backup
- B . A phone tree used to contact necessary personnel
- C . A script used to verify patches are installed on systems
- D . An IPS rule that prevents web access from international locations
Latest GCCC Dumps Valid Version with 93 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

