GAQM CPEH-001 Certified Professional Ethical Hacker (CPEH) Online Training
GAQM CPEH-001 Online Training
The questions for CPEH-001 were last updated at Apr 17,2026.
- Exam Code: CPEH-001
- Exam Name: Certified Professional Ethical Hacker (CPEH)
- Certification Provider: GAQM
- Latest update: Apr 17,2026
Which of the following is considered as one of the most reliable forms of TCP scanning?
- A . TCP Connect/Full Open Scan
- B . Half-open Scan
- C . NULL Scan
- D . Xmas Scan
Which of the following scanning method splits the TCP header into several packets and makes it difficult for packet filters to detect the purpose of the packet?
- A . ICMP Echo scanning
- B . SYN/FIN scanning using IP fragments
- C . ACK flag probe scanning
- D . IPID scanning
What is the purpose of a demilitarized zone on a network?
- A . To scan all traffic coming through the DMZ to the internal network
- B . To only provide direct access to the nodes within the DMZ and protect the network behind it
- C . To provide a place to put the honeypot
- D . To contain the network devices you wish to protect
You need to deploy a ned needs to be available on the Internet.
What is the recommended architecture in terms of server placement?
- A . All three servers need to be placed internally
- B . A web server facing the Internet, an application server on the internal network, a database server on the internal network
- C . A web server and the database server facing the Internet, an application server on the internal network
- D . All three servers need tw web-based software package for your organization. The package requires three separate servers an
o face the Internet so that they can communicate between themselves
The security administrator of ABC needs to permit Internet traffic in the host 10.0.0.2 and UDP traffic in the host 10.0.0.3. He also needs to permit all FTP traffic to the rest of the network and deny all other traffic. After he applied his ACL configuration in the router, nobody can access to the ftp, and the permitted hosts cannot access the Internet.
According to the next configuration, what is happening in the network?
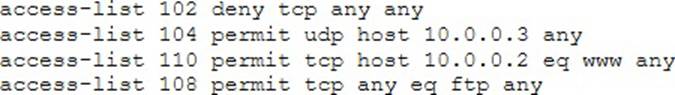
- A . The ACL 104 needs to be first because is UDP
- B . The ACL 110 needs to be changed to port 80
- C . The ACL for FTP must be before the ACL 110
- D . The first ACL is denying all TCP traffic and the other ACLs are being ignored by the router
When conducting a penetration test, it is crucial to use all means to get all available information about the target network. One of the ways to do that is by sniffing the network.
Which of the following cannot be performed by the passive network sniffing?
- A . Identifying operating systems, services, protocols and devices
- B . Modifying and replaying captured network traffic
- C . Collecting unencrypted information about usernames and passwords
- D . Capturing a network traffic for further analysis
Insecure direct object reference is a type of vulnerability where the application does not verify if the user is authorized to access the internal object via its name or key.
Suppose a malicious user Rob tries to get access to the account of a benign user Ned.
Which of the following requests best illustrates an attempt to exploit an insecure direct object reference vulnerability?
- A . “GET/restricted/goldtransfer?to=Rob&from=1 or 1=1’ HTTP/1.1Host: westbank.com”
- B . “GET/restricted/accounts/?name=Ned HTTP/1.1 Host: westbank.com”
- C . “GET/restricted/bank.getaccount(‘Ned’) HTTP/1.1 Host: westbank.com”
- D . “GET/restricted/r
%00account%00Ned%00access HTTP/1.1 Host: westbank.com”
What type of vulnerability/attack is it when the malicious person forces the user’s browser to send an authenticated request to a server?
- A . Cross-site request forgery
- B . Cross-site scripting
- C . Session hijacking
- D . Server side request forgery
From the following table, identify the wrong answer in terms of Range (ft).
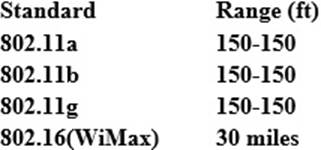
- A . 802.11b
- B . 802.11g
- C . 802.16(WiMax)
- D . 802.11a
What would you enter, if you wanted to perform a stealth scan using Nmap?
- A . nmap -sU
- B . nmap -sS
- C . nmap -sM
- D . nmap -sT
Latest CPEH-001 Dumps Valid Version with 736 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

