Fortinet NSE6_FAC-6.4 Fortinet NSE 6 – FortiAuthenticator 6.4 Online Training
Fortinet NSE6_FAC-6.4 Online Training
The questions for NSE6_FAC-6.4 were last updated at Apr 21,2025.
- Exam Code: NSE6_FAC-6.4
- Exam Name: Fortinet NSE 6 - FortiAuthenticator 6.4
- Certification Provider: Fortinet
- Latest update: Apr 21,2025
Examine the screenshot shown in the exhibit.
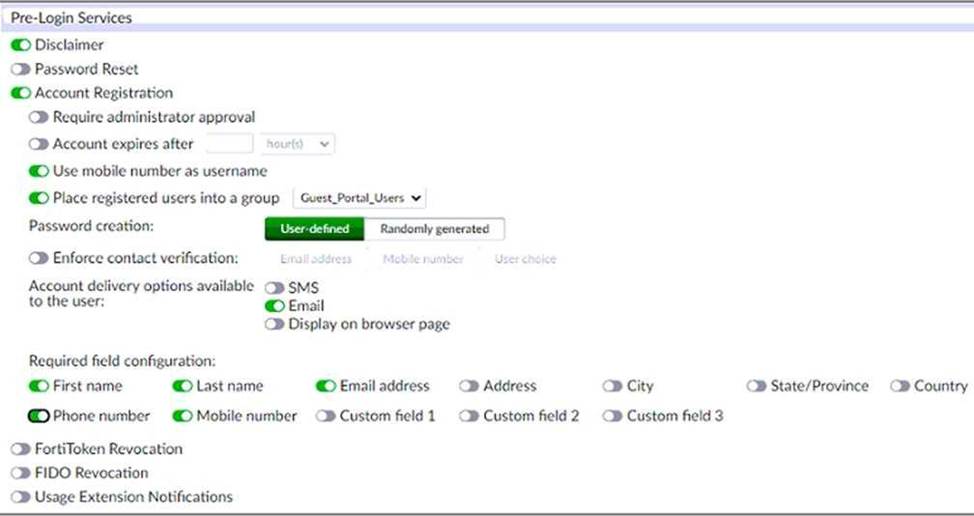
Which two statements regarding the configuration are true? (Choose two.)
- A . All guest accounts created using the account registration feature will be placed under the Guest_Portal_Users group
- B . All accounts registered through the guest portal must be validated through email
- C . Guest users must fill in all the fields on the registration form
- D . Guest user account will expire after eight hours
A, B
Explanation:
The screenshot shows that the account registration feature is enabled for the guest portal and that the guest group is set to Guest_Portal_Users. This means that all guest accounts created using this feature will be placed under that group1. The screenshot also shows that email validation is enabled for the guest portal and that the email validation link expires after 24 hours. This means that all accounts registered through the guest portal must be validated through email within that time frame1.
Reference: 1 https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/guest-management#account-registration
An administrator is integrating FortiAuthenticator with an existing RADIUS server with the intent of eventually replacing the RADIUS server with FortiAuthenticator.
How can FortiAuthenticator help facilitate this process?
- A . By configuring the RADIUS accounting proxy
- B . By enabling automatic REST API calls from the RADIUS server
- C . By enabling learning mode in the RADIUS server configuration
- D . By importing the RADIUS user records
C
Explanation:
FortiAuthenticator can help facilitate the process of replacing an existing RADIUS server by enabling learning mode in the RADIUS server configuration. This allows FortiAuthenticator to learn user credentials from the existing RADIUS server and store them locally for future authentication requests2. This way, FortiAuthenticator can gradually take over the role of the RADIUS server without disrupting the user experience.
Reference: 2 https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/radius-service#learning-mode
You are an administrator for a large enterprise and you want to delegate the creation and management of guest users to a group of sponsors.
How would you associate the guest accounts with individual sponsors?
- A . As an administrator, you can assign guest groups to individual sponsors.
- B . Guest accounts are associated with the sponsor that creates the guest account.
- C . You can automatically add guest accounts to groups associated with specific sponsors.
- D . Select the sponsor on the guest portal, during registration.
B
Explanation:
Guest accounts are associated with the sponsor that creates the guest account. A sponsor is a user who has permission to create and manage guest accounts on behalf of other users3. A sponsor can create guest accounts using the sponsor portal or the REST API3. The sponsor’s username is recorded as a field in the guest account’s profile3.
Reference: 3 https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/guest-management#sponsors
You are a Wi-Fi provider and host multiple domains.
How do you delegate user accounts, user groups and permissions per domain when they are authenticating on a single FortiAuthenticator device?
- A . Create realms.
- B . Create user groups
- C . Create multiple directory trees on FortiAuthenticator
- D . Automatically import hosts from each domain as they authenticate.
A
Explanation:
Realms are a way to delegate user accounts, user groups and permissions per domain when they are authenticating on a single FortiAuthenticator device. A realm is a logical grouping of users and groups based on a common attribute, such as a domain name or an IP address range. Realms allow administrators to apply different authentication policies and settings to different groups of users based on their realm membership.
Reference: https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/user-management#realms
You have implemented two-factor authentication to enhance security to sensitive enterprise systems.
How could you bypass the need for two-factor authentication for users accessing form specific secured networks?
- A . Create an admin realm in the authentication policy
- B . Specify the appropriate RADIUS clients in the authentication policy
- C . Enable Adaptive Authentication in the portal policy
- D . Enable the Resolve user geolocation from their IP address option in the authentication policy.
C
Explanation:
Adaptive Authentication is a feature that allows administrators to bypass the need for two-factor authentication for users accessing from specific secured networks. Adaptive Authentication uses geolocation information from IP addresses to determine whether a user is accessing from a trusted network or not. If the user is accessing from a trusted network, FortiAuthenticator can skip the second factor of authentication and grant access based on the first factor only.
Reference: https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/authentication-policies#adaptive-authentication
Which network configuration is required when deploying FortiAuthenticator for portal services?
- A . FortiAuthenticator must have the REST API access enable on port1
- B . One of the DNS servers must be a FortiGuard DNS server
- C . Fortigate must be setup as default gateway for FortiAuthenticator
- D . Policies must have specific ports open between FortiAuthenticator and the authentication clients
D
Explanation:
When deploying FortiAuthenticator for portal services, such as guest portal, sponsor portal, user portal or FortiToken activation portal, the network configuration must allow specific ports to be open between FortiAuthenticator and the authentication clients.
These ports are:
TCP 80 for HTTP access
TCP 443 for HTTPS access
TCP 389 for LDAP access
TCP 636 for LDAPS access
UDP 1812 for RADIUS authentication
UDP 1813 for RADIUS accounting
Reference: https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/portal-services#network-configuration
You are a FortiAuthenticator administrator for a large organization. Users who are configured to use FortiToken 200 for two-factor authentication can no longer authenticate. You have verified that only the users with two-factor authentication are experiencing the issue.
What can cause this issue?
- A . FortiToken 200 license has expired
- B . One of the FortiAuthenticator devices in the active-active cluster has failed
- C . Time drift between FortiAuthenticator and hardware tokens
- D . FortiAuthenticator has lost contact with the FortiToken Cloud servers
C
Explanation:
One possible cause of the issue is time drift between FortiAuthenticator and hardware tokens. Time drift occurs when the internal clocks of FortiAuthenticator and hardware tokens are not synchronized. This can result in mismatched one-time passwords (OTPs) generated by the hardware tokens and expected by FortiAuthenticator. To prevent this issue, FortiAuthenticator provides a time drift tolerance option that allows a certain number of seconds of difference between the clocks.
Reference: https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/two-factor-authentication#time-drift-tolerance
Why would you configure an OCSP responder URL in an end-entity certificate?
- A . To designate the SCEP server to use for CRL updates for that certificate
- B . To identify the end point that a certificate has been assigned to
- C . To designate a server for certificate status checking
- D . To provide the CRL location for the certificate
C
Explanation:
An OCSP responder URL in an end-entity certificate is used to designate a server for certificate status checking. OCSP stands for Online Certificate Status Protocol, which is a method of verifying whether a certificate is valid or revoked in real time. An OCSP responder is a server that responds to OCSP requests from clients with the status of the certificate in question. The OCSP responder URL in an end-entity certificate points to the location of the OCSP responder that can provide the status of that certificate.
Reference: https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/certificate-management#ocsp-responder
An administrator wants to keep local CA cryptographic keys stored in a central location.
Which FortiAuthenticator feature would provide this functionality?
- A . SCEP support
- B . REST API
- C . Network HSM
- D . SFTP server
C
Explanation:
Network HSM is a feature that allows FortiAuthenticator to keep local CA cryptographic keys stored in a central location. HSM stands for Hardware Security Module, which is a physical device that provides secure storage and generation of cryptographic keys. Network HSM allows FortiAuthenticator to use an external HSM device to store and manage the private keys of its local CAs, instead of storing them locally on the FortiAuthenticator device.
Reference: https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/certificate-management#network-hsm
Which option correctly describes an SP-initiated SSO SAML packet flow for a host without a SAML assertion?
- A . Service provider contacts idendity provider, idendity provider validates principal for service provider, service provider establishes communication with principal
- B . Principal contacts idendity provider and is redirected to service provider, principal establishes connection with service provider, service provider validates authentication with identify provider
- C . Principal contacts service provider, service provider redirects principal to idendity provider, after succesfull authentication identify provider redirects principal to service provider
- D . Principal contacts idendity provider and authenticates, identity provider relays principal to service provider after valid authentication
C
Explanation:
SP-initiated SSO SAML packet flow for a host without a SAML assertion is as follows:
Principal contacts service provider, requesting access to a protected resource.
Service provider redirects principal to identity provider, sending a SAML authentication request.
Principal authenticates with identity provider using their credentials.
After successful authentication, identity provider redirects principal back to service provider, sending a SAML response with a SAML assertion containing the principal’s attributes.
Service provider validates the SAML response and assertion, and grants access to the principal.
Reference: https://docs.fortinet.com/document/fortiauthenticator/6.4.0/administration-guide/906179/saml-service-provider#sp-initiated-sso
Latest NSE6_FAC-6.4 Dumps Valid Version with 47 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

