Fortinet NSE4_FGT-7.0 Fortinet NSE 4 – FortiOS 7.0 Online Training
Fortinet NSE4_FGT-7.0 Online Training
The questions for NSE4_FGT-7.0 were last updated at Apr 15,2025.
- Exam Code: NSE4_FGT-7.0
- Exam Name: Fortinet NSE 4 - FortiOS 7.0
- Certification Provider: Fortinet
- Latest update: Apr 15,2025
When configuring a firewall virtual wire pair policy, which following statement is true?
- A . Any number of virtual wire pairs can be included, as long as the policy traffic direction is the same.
- B . Only a single virtual wire pair can be included in each policy.
- C . Any number of virtual wire pairs can be included in each policy, regardless of the policy traffic direction settings.
- D . Exactly two virtual wire pairs need to be included in each policy.
A
Explanation:
Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=FD48690
Refer to the exhibit.
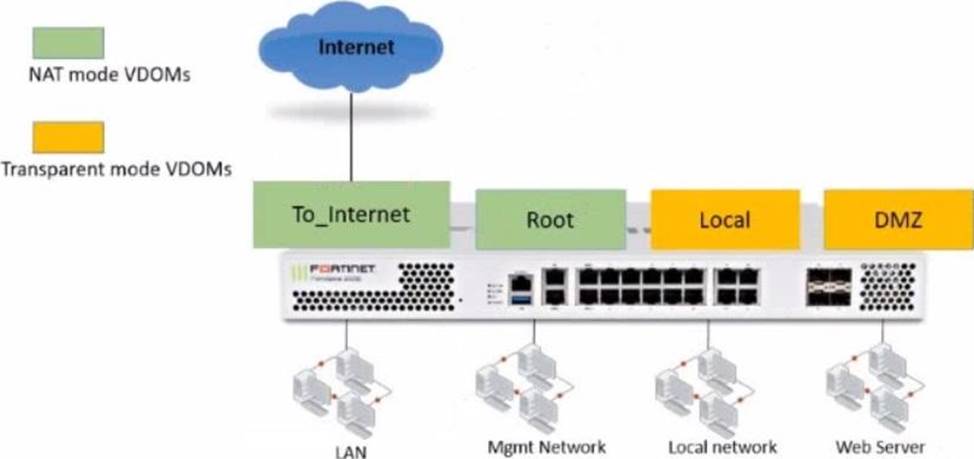
The Root and To_Internet VDOMs are configured in NAT mode. The DMZ and Local VDOMs are configured in transparent mode.
The Root VDOM is the management VDOM. The To_Internet VDOM allows LAN users to access the internet. The To_Internet VDOM is the only VDOM with internet access and is directly connected to ISP modem.
With this configuration, which statement is true?
- A . Inter-VDOM links are required to allow traffic between the Local and Root VDOMs.
- B . A static route is required on the To_Internet VDOM to allow LAN users to access the internet.
- C . Inter-VDOM links are required to allow traffic between the Local and DMZ VDOMs.
- D . Inter-VDOM links are not required between the Root and To_Internet VDOMs because the Root VDOM is used only as a management VDOM.
A
Explanation:
Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=FD46542
Refer to the exhibit.
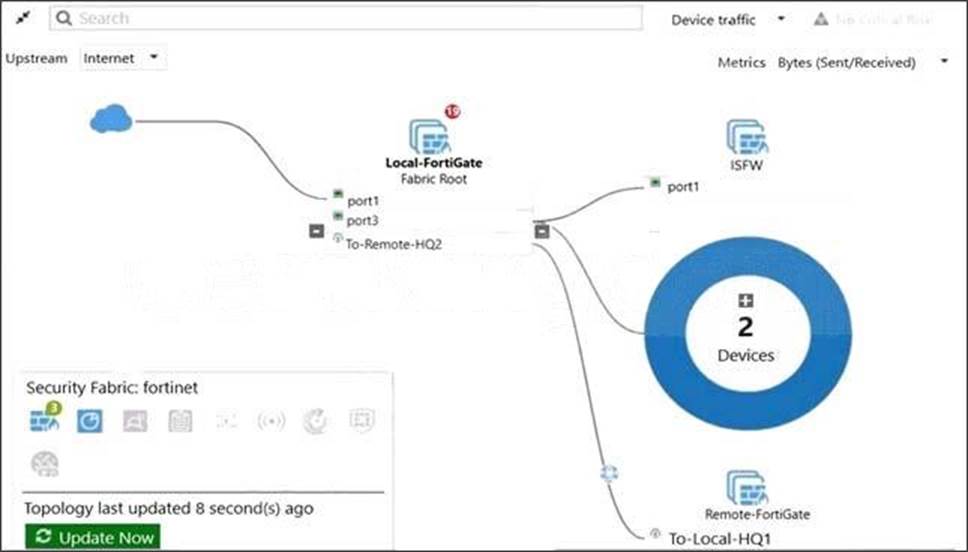
Given the security fabric topology shown in the exhibit, which two statements are true? (Choose two.)
- A . There are five devices that are part of the security fabric.
- B . Device detection is disabled on all FortiGate devices.
- C . This security fabric topology is a logical topology view.
- D . There are 19 security recommendations for the security fabric.
C,D
Explanation:
References:
https://docs.fortinet.com/document/fortigate/5.6.0/cookbook/761085/results
https://docs.fortinet.com/document/fortimanager/6.2.0/new-features/736125/security-fabric-topology
Refer to the exhibit.
Exhibit A.
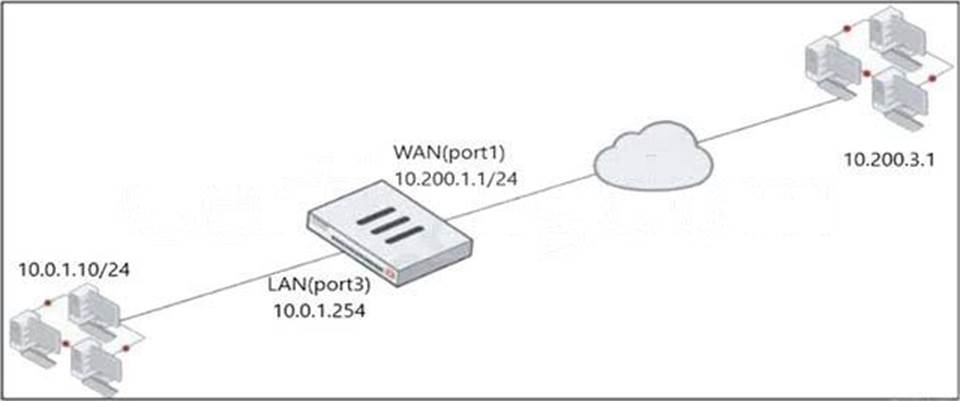
Exhibit B.
The exhibit contains a network diagram, virtual IP, IP pool, and firewall policies configuration.
The WAN (port1) interface has the IP address 10.200.1.1/24.
The LAN (port3) interface has the IP address 10 .0.1.254. /24.
The first firewall policy has NAT enabled using IP Pool.
The second firewall policy is configured with a VIP as the destination address.
Which IP address will be used to source NAT the internet traffic coming from a workstation with the IP address 10.0.1.10?
- A . 10.200.1.1
- B . 10.200.3.1
- C . 10.200.1.100
- D . 10.200.1.10
A
Explanation:
Reference: https://help.fortinet.com/fos60hlp/60/Content/FortiOS/fortigate-firewall/Concepts%20-%20Firewall/Static%20NAT.htm
https://kb.fortinet.com/kb/documentLink.do?externalID=FD44529
Refer to the exhibit.
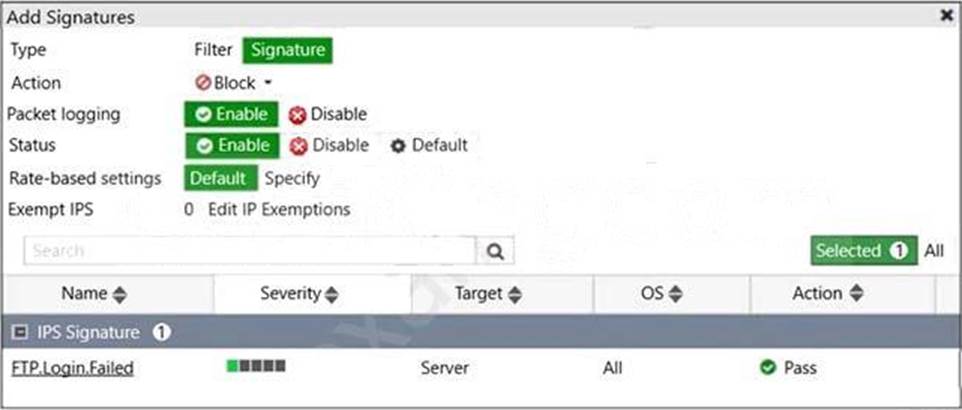
Review the Intrusion Prevention System (IPS) profile signature settings.
Which statement is correct in adding the FTP.Login.Failed signature to the IPS sensor profile?
- A . The signature setting uses a custom rating threshold.
- B . The signature setting includes a group of other signatures.
- C . Traffic matching the signature will be allowed and logged.
- D . Traffic matching the signature will be silently dropped and logged.
D
Explanation:
Action is drop, signature default action is listed only in the signature, it would only match if action was set to default.
Which engine handles application control traffic on the next-generation firewall (NGFW) FortiGate?
- A . Antivirus engine
- B . Intrusion prevention system engine
- C . Flow engine
- D . Detection engine
B
Explanation:
Reference: http://docs.fortinet.com/document/fortigate/6.0.0/handbook/240599/application-control
Refer to the exhibit.
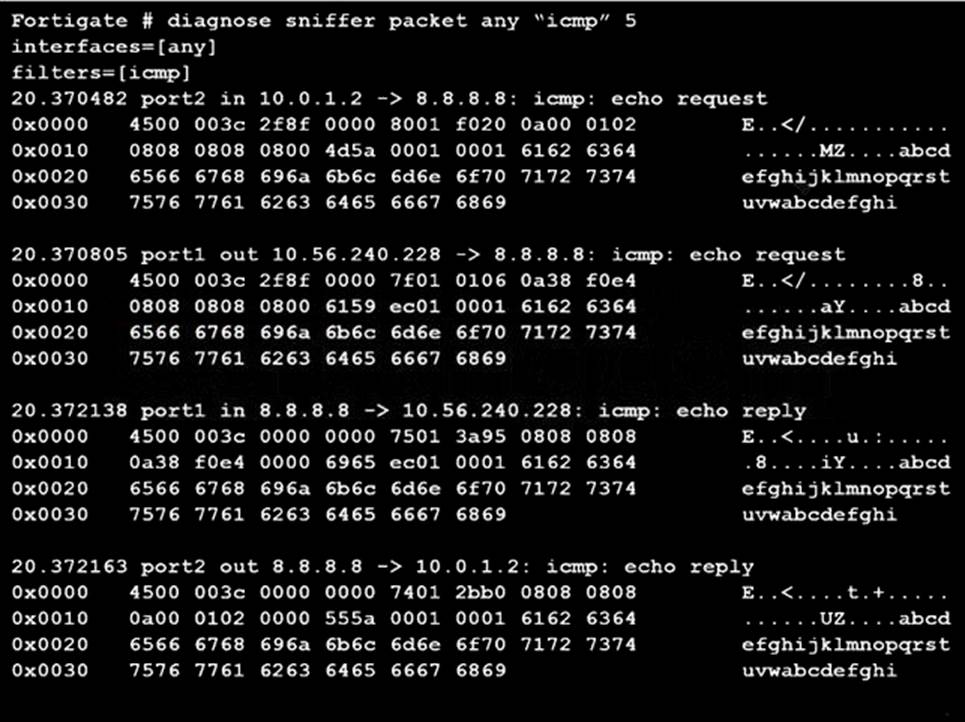
An administrator is running a sniffer command as shown in the exhibit.
Which three pieces of information are included in the sniffer output? (Choose three.)
- A . Interface name
- B . Ethernet header
- C . IP header
- D . Application header
- E . Packet payload
A,C,E
Explanation:
Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=11186
Refer to the exhibit.
Exhibit A.
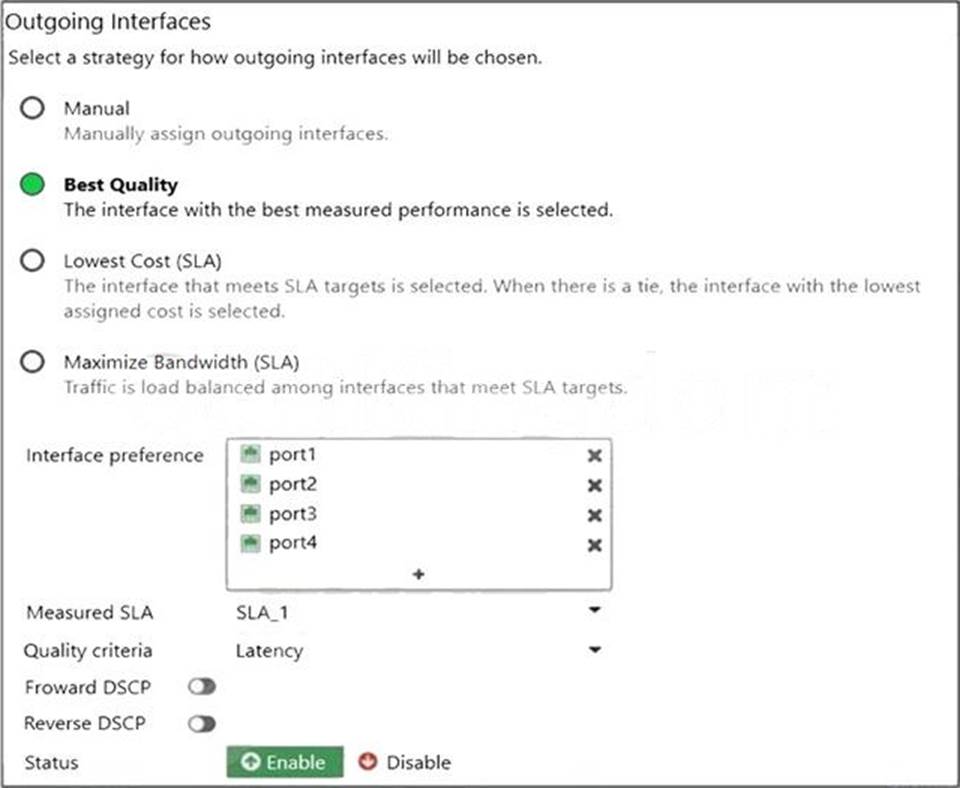
Exhibit B.
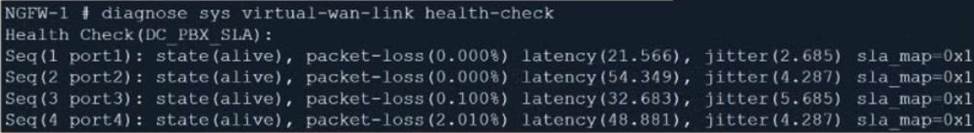
The exhibit contains the configuration for an SD-WAN Performance SLA, as well as the output of diagnose sys virtual-wan-link health-check.
Which interface will be selected as an outgoing interface?
- A . port2
- B . port4
- C . port3
- D . port1
D
Explanation:
Port 1 shows the lowest latency.
A network administrator has enabled SSL certificate inspection and antivirus on FortiGate. When downloading an EICAR test file through HTTP, FortiGate detects the virus and blocks the file. When downloading the same file through HTTPS, FortiGate does not detect the virus and the file can be downloaded.
What is the reason for the failed virus detection by FortiGate?
- A . Application control is not enabled
- B . SSL/SSH Inspection profile is incorrect
- C . Antivirus profile configuration is incorrect
- D . Antivirus definitions are not up to date
B
Explanation:
https traffic requires SSL decryption. Check the ssh inspection profile
An administrator does not want to report the logon events of service accounts to FortiGate.
What setting on the collector agent is required to achieve this?
- A . Add the support of NTLM authentication.
- B . Add user accounts to Active Directory (AD).
- C . Add user accounts to the FortiGate group fitter.
- D . Add user accounts to the Ignore User List.
D
Explanation:
Reference: https://kb.fortinet.com/kb/documentLink.do?externalID=FD38828
Latest NSE4_FGT-7.0 Dumps Valid Version with 172 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

