Check Point 156-215.80 Check Point Certified Security Administrator R80 Online Training
Check Point 156-215.80 Online Training
The questions for 156-215.80 were last updated at Apr 22,2025.
- Exam Code: 156-215.80
- Exam Name: Check Point Certified Security Administrator R80
- Certification Provider: Check Point
- Latest update: Apr 22,2025
Which of the following is NOT an integral part of VPN communication within a network?
- A . VPN key
- B . VPN community
- C . VPN trust entities
- D . VPN domain
Two administrators Dave and Jon both manage R80 Management as administrators for ABC Corp. Jon logged into the R80 Management and then shortly after Dave logged in to the same server. They are both in the Security Policies view.
From the screenshots below, why does Dave not have the rule no.6 in his SmartConsole view even though Jon has it his in his SmartConsole view?
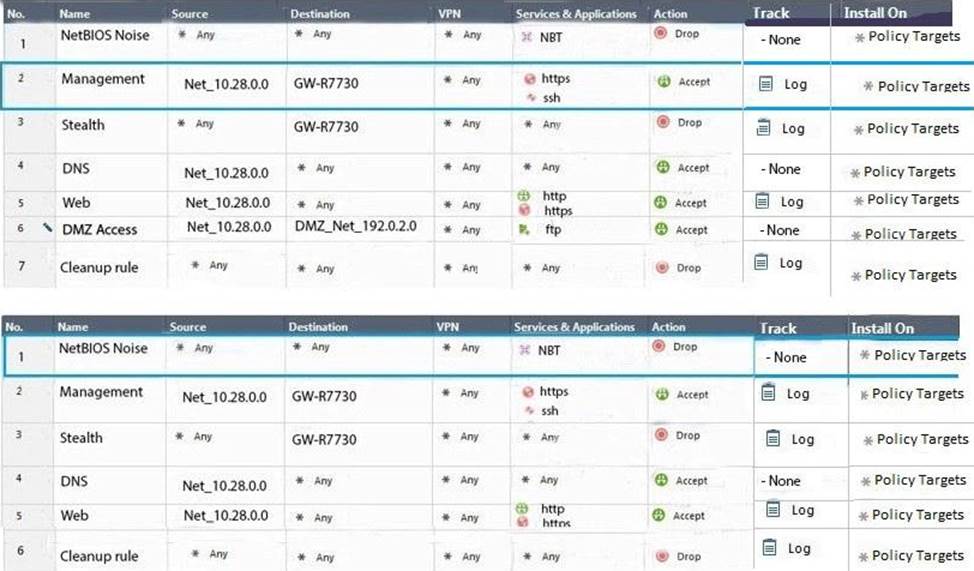
- A . Jon is currently editing rule no.6 but has Published part of his changes.
- B . Dave is currently editing rule no.6 and has marked this rule for deletion.
- C . Dave is currently editing rule no.6 and has deleted it from his Rule Base.
- D . Jon is currently editing rule no.6 but has not yet Published his changes.
Vanessa is firewall administrator in her company; her company is using Check Point firewalls on central and remote locations, which are managed centrally by R80 Security Management Server. One central location has an installed R77.30 Gateway on Open server. Remote location is using Check Point UTM-1 570 series appliance with R71.
Which encryption is used in Secure Internal Communication (SIC) between central management and firewall on each location?
- A . On central firewall AES128 encryption is used for SIC, on Remote firewall 3DES encryption is used for SIC.
- B . On both firewalls, the same encryption is used for SIC. This is AES-GCM-256.
- C . The Firewall Administrator can choose which encryption suite will be used by SIC.
- D . On central firewall AES256 encryption is used for SIC, on Remote firewall AES128 encryption is used for SIC.
Review the following screenshot and select the BEST answer.

- A . Data Center Layer is an inline layer in the Access Control Policy.
- B . By default all layers are shared with all policies.
- C . If a connection is dropped in Network Layer, it will not be matched against the rules in Data Center Layer.
- D . If a connection is accepted in Network-layer, it will not be matched against the rules in Data Center Layer.
Which of the following is NOT a SecureXL traffic flow?
- A . Medium Path
- B . Accelerated Path
- C . High Priority Path
- D . Slow Path
Which of the following Automatically Generated Rules NAT rules have the lowest implementation priority?
- A . Machine Hide NAT
- B . Address Range Hide NAT
- C . Network Hide NAT
- D . Machine Static NAT
Which of the following Automatically Generated Rules NAT rules have the lowest implementation priority?
- A . Machine Hide NAT
- B . Address Range Hide NAT
- C . Network Hide NAT
- D . Machine Static NAT
Which of the following Automatically Generated Rules NAT rules have the lowest implementation priority?
- A . Machine Hide NAT
- B . Address Range Hide NAT
- C . Network Hide NAT
- D . Machine Static NAT
Which of the following Automatically Generated Rules NAT rules have the lowest implementation priority?
- A . Machine Hide NAT
- B . Address Range Hide NAT
- C . Network Hide NAT
- D . Machine Static NAT
Which of the following Automatically Generated Rules NAT rules have the lowest implementation priority?
- A . Machine Hide NAT
- B . Address Range Hide NAT
- C . Network Hide NAT
- D . Machine Static NAT
Latest 156-215.80 Dumps Valid Version with 528 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

