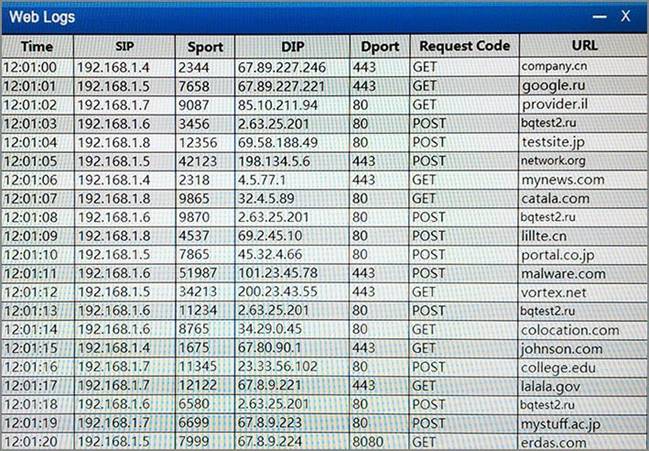
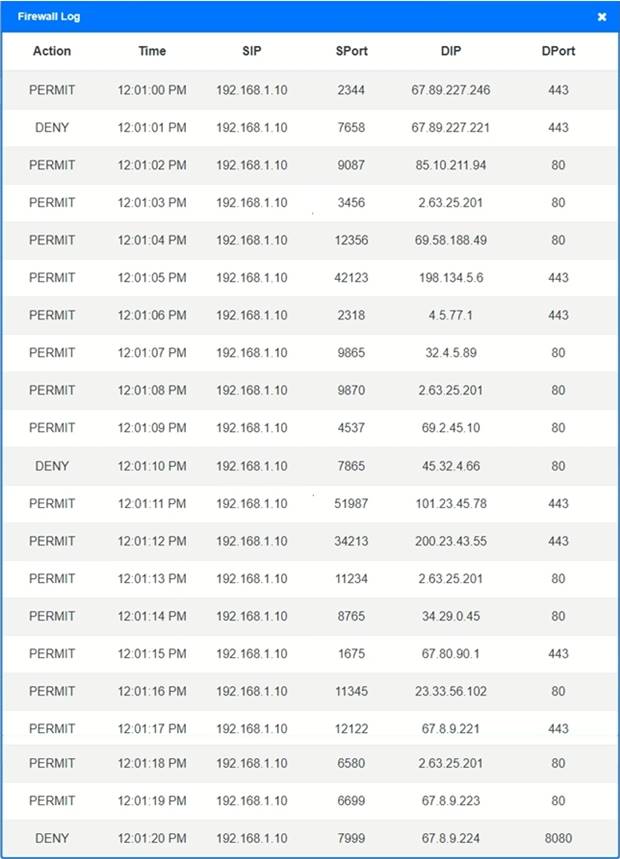
A security analyst suspects that a workstation may be beaconing to a command and control server. Inspect the logs from the company’s web proxy server and the firewall to determine the best course of action to take in order to neutralize the threat with minimum impact to the organization
HOTSPOT
A security analyst suspects that a workstation may be beaconing to a command and control server. Inspect the logs from the company’s web proxy server and the firewall to determine the best course of action to take in order to neutralize the threat with minimum impact to the organization.
Instructions:
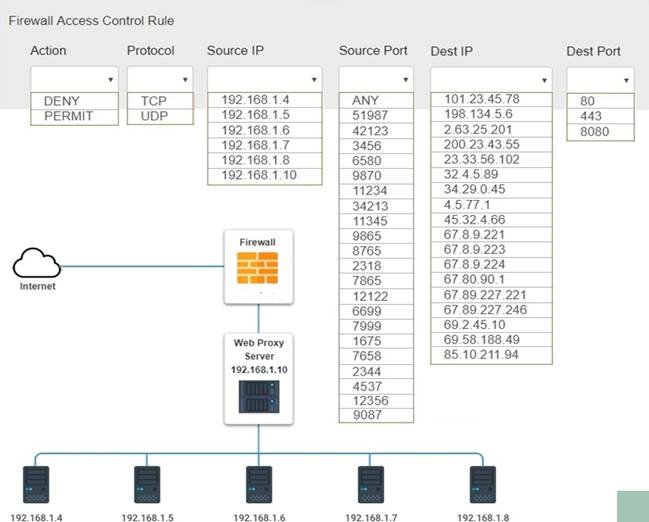
Modify the firewall ACL, using the Firewall ACL form to mitigate the issue.
If at any time you would like to bring back the initial state of the simulation, please select the Reset All button.
Answer: 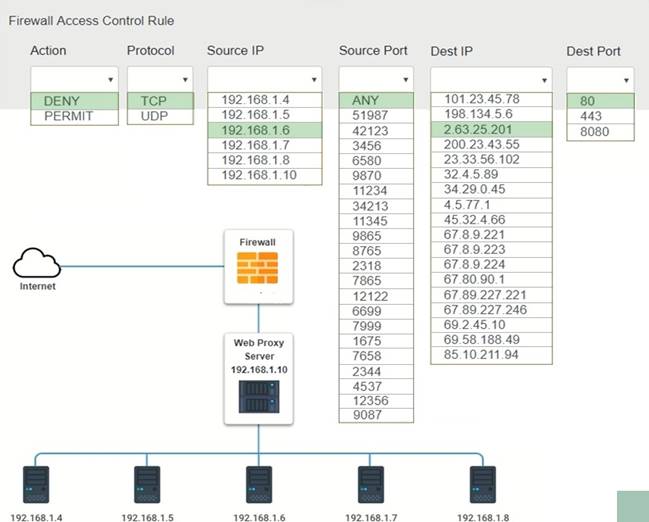
Latest CS0-001 Dumps Valid Version with 455 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund


Shouldn’t the src be 192.168.1.10?
Because all web traffic are proxied before hitting the firewall.