Drag and drop the cryptographic algorithms for IPsec from the left onto the correct cryptographic processes on the right
DRAG DROP
Drag and drop the cryptographic algorithms for IPsec from the left onto the correct cryptographic processes on the right.
Answer: 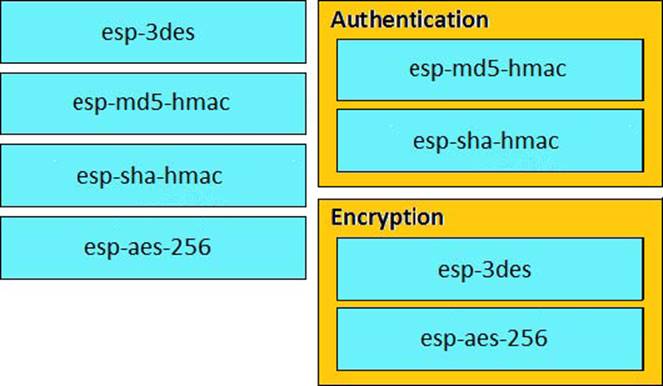
Explanation:
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/sec_conn_vpnips/configuration/xe3s/sec-sec-for-vpns-w-ipsec-xe-3s-book/sec-cfg-vpn-ipsec.html
Latest 300-209 Dumps Valid Version with 394 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund
Subscribe
Login
0 Comments
Inline Feedbacks
View all comments

