CyberArk SECRET-SEN CyberArk Sentry Secrets Manager Online Training
CyberArk SECRET-SEN Online Training
The questions for SECRET-SEN were last updated at Feb 09,2026.
- Exam Code: SECRET-SEN
- Exam Name: CyberArk Sentry Secrets Manager
- Certification Provider: CyberArk
- Latest update: Feb 09,2026
When working with Summon, what is the purpose of the secrets.yml file?
- A . It is where Summon outputs the secret value after retrieval.
- B . It is where you define which secrets to retrieve.
- C . It is where you store the Conjur URL and host API key.
- D . It is the log file for Summon.
You are deploying Kubernetes resources/objects as Conjur identities.
In addition to Namespace and Deployment, from which options can you choose? (Choose two.)
- A . ServiceAccount
- B . Replica sets
- C . Secrets
- D . Tokenreviews
- E . StatefulSet
You modified a Conjur host policy to change its annotations for authentication.
How should you load the policy to make those changes?
- A . Use the default “append” method (e.g. conjur policy load <branch> <policy-file>).
- B . Use the “replace” method (e.g. conjur policy load C Creplace <branch> <policy-file>).
- C . Use the “delete” method (e.g. conjur policy load C Cdelete <branch> <policy-file>).
- D . Use the “update” method (e.g. conjur policy load C Cupdate <branch> <policy-file>).
When installing the Vault Conjur Synchronizer, you see this error:
– Forbidden
– Logon Token is Empty C Cannot logon
– Unauthorized
What must you ensure to remediate the issue?
- A . This admin user must not be logged in to other sessions during the Vault Conjur Synchronizer installation process.
- B . You specified the correct url for Conjur and it is listed as a SAN on that url’s certificate.
- C . You correctly URI encoded the url in the installation script.
- D . You ran powershell as Administrator and there is sufficient space on the server on which you are running the installation.
Refer to the exhibit.
![]()
In which example will auto-failover occur?
A)
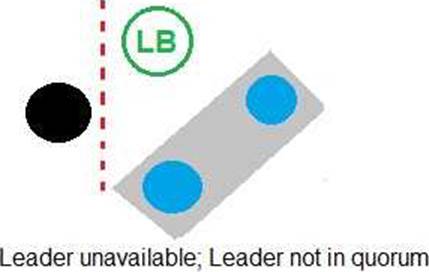
B)
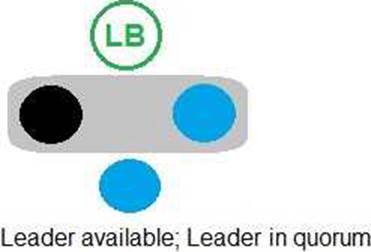
C)

D)
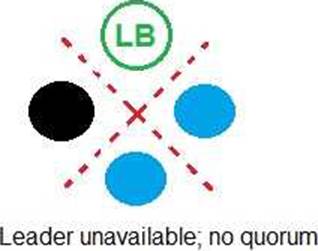
- A . Option A
- B . Option B
- C . Option C
- D . Option D
An application is having authentication issues when trying to securely retrieve credential’s from the Vault using the CCP webservices RESTAPI. CyberArk Support advised that further debugging should be enabled on the CCP server to output a trace file to review detailed logs to help isolate the problem.
What best describes how to enable debug for CCP?
- A . Edit web.config. change the “AIMWebServiceTrace” value, restart Windows Web Server (IIS)
- B . In the PVWA, go to the Applications tab, select the Application in question, go to Options > Logging and choose Debug.
- C . From the command line, run appprvmgr.exe update_config logging=debug.
- D . Edit the basic_appprovider.conf, change the “AIMWebServiceTrace" value, and restart the provider.
When working with Credential Providers in a Privileged Cloud setting, what is a special consideration?
- A . If there are installation issues, troubleshooting may need to involve the Privileged Cloud support team.
- B . Credential Providers are not supported in a Privileged Cloud setting.
- C . The AWS Cloud account number must be defined in the file main appprovider.conf. <platform>.<version> found in the AppProviderConf Safe.
- D . Debug logging for Credential Providers deployed in a Privileged Cloud setting can inadvertently exhaust available disk space.
While retrieving a secret through REST, the secret retrieval fails to find a matching secret. You know the secret onboarding process was completed, the secret is in the expected safe with the expected object name, and the CCP is able to provide secrets to other applications.
What is the most likely cause for this issue?
- A . The application ID or Application Provider does not have the correct permissions on the safe.
- B . The client certificate fingerprint is not trusted.
- C . The service account running the application does not have the correct permissions on the safe.
- D . The OS user does not have the correct permissions on the safe
You are setting up a Kubernetes integration with Conjur. With performance as the key deciding factor, namespace and service account will be used as identity characteristics.
Which authentication method should you choose?
- A . JWT-based authentication
- B . Certificate-based authentication
- C . API key authentication
- D . Connect (OIDC) authentication
When attempting to retrieve a credential, you receive an error 401 C Malformed Authorization Token.
What is the cause of the issue?
- A . The token is not correctly encoded.
- B . The token you are trying to retrieve does not exist.
- C . The host does not have access to the credential with the current token.
- D . The credential has not been initialized.
Latest SECRET-SEN Dumps Valid Version with 60 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund

