CyberArk EPM-DEF CyberArk Defender – EPM Online Training
CyberArk EPM-DEF Online Training
The questions for EPM-DEF were last updated at Feb 08,2026.
- Exam Code: EPM-DEF
- Exam Name: CyberArk Defender - EPM
- Certification Provider: CyberArk
- Latest update: Feb 08,2026
A Helpdesk technician needs to provide remote assistance to a user whose laptop cannot connect to the Internet to pull EPM policies.
What CyberArk EPM feature should the Helpdesk technician use to allow the user elevation capabilities?
- A . Offline Policy Authorization Generator
- B . Elevate Trusted Application If Necessary
- C . Just In Time Access and Elevation
- D . Loosely Connected Devices Credential Management
Which policy can be used to improve endpoint performance for applications commonly used for software development?
- A . Developer Applications
- B . Trusted Application
- C . Trusted Source
- D . Software Updater
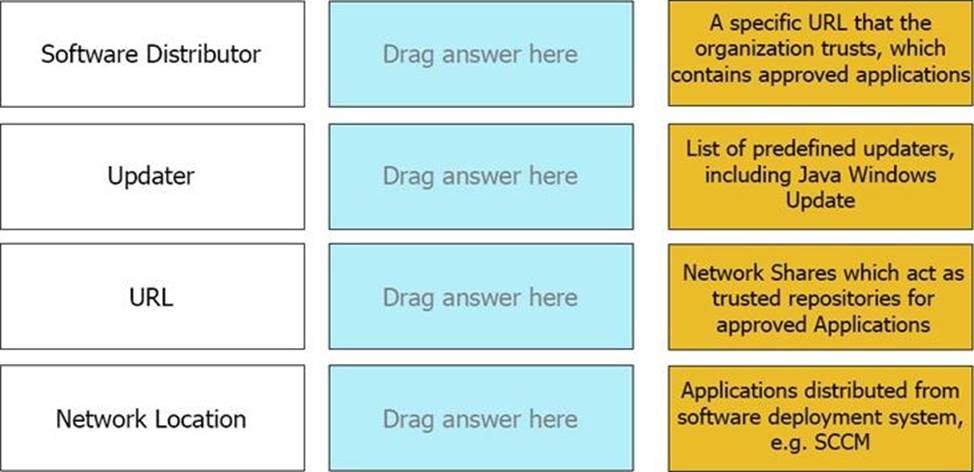
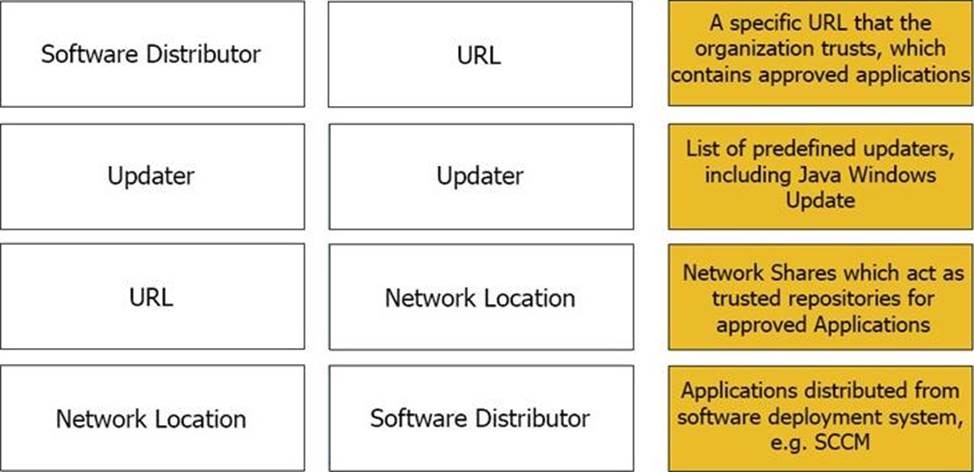
Which of the following application options can be used when defining trusted sources?
- A . Publisher, Product, Size, URL
- B . Publisher, Name, Size, URI
- C . Product, URL, Machine, Package
- D . Product, Publisher, User/Group, Installation Package
An EPM Administrator is looking to enable the Threat Deception feature, under what section should the EPM Administrator go to enable this feature?
- A . Threat Protection Inbox
- B . Policies
- C . Threat Intelligence
- D . Policy Audit
An EPM Administrator would like to enable CyberArk EPM’s Ransomware Protection in Restrict mode.
What should the EPM Administrator do?
- A . Set Block unhandled applications to On.
- B . Set Protect Against Ransomware to Restrict.
- C . Set Protect Against Ransomware to Restrict and Set Block unhandled applications to On.
- D . Set Control unhandled applications to Detect.
An EPM Administrator would like to enable a Threat Protection policy, however, the policy protects an application that is not installed on all endpoints.
What should the EPM Administrator do?
- A . Enable the Threat Protection policy and configure the Policy Targets.
- B . Do not enable the Threat Protection policy.
- C . Enable the Threat Protection policy only in Detect mode.
- D . Split up the endpoints in to separate Sets and enable Threat Protection for only one of the Sets.
After a clean installation of the EPM agent, the local administrator password is not being changed on macOS and the old password can still be used to log in.
What is a possible cause?
- A . Secure Token on macOS endpoint is not enabled.
- B . EPM agent is not able to connect to the EPM server.
- C . After installation, Full Disk Access for the macOS agent to support EPM policies was not approved.
- D . Endpoint password policy is too restrictive.
In EPM, creation of which user type is required to use SAML?
- A . Local CyberArk EPM User
- B . AD User
- C . SQL User
- D . Azure AD User
A company is looking to manage their Windows Servers and Desktops with CyberArk EPM. Management would like to define different default policies between the Windows Servers and Windows Desktops.
What should the EPM Administrator do?
- A . In the Default Policies, exclude either the Windows Servers or the Windows Desktops.
- B . Create Advanced Policies to apply different policies between Windows Servers and Windows Desktops.
- C . CyberArk does not recommend installing EPM Agents on Windows Servers.
- D . Create a separate Set for Windows Servers and Windows Desktops.
Latest EPM-DEF Dumps Valid Version with 60 Q&As
Latest And Valid Q&A | Instant Download | Once Fail, Full Refund